Every successful interview starts with knowing what to expect. In this blog, we’ll take you through the top Public-key infrastructure (PKI) interview questions, breaking them down with expert tips to help you deliver impactful answers. Step into your next interview fully prepared and ready to succeed.
Questions Asked in Public-key infrastructure (PKI) Interview
Q 1. Explain the components of a Public Key Infrastructure (PKI).
A Public Key Infrastructure (PKI) is a system for creating, managing, distributing, using, storing, and revoking digital certificates and managing public-key cryptography. Think of it as a digital trust system. It’s built on several key components working together:
- Certificate Authority (CA): The trusted entity that issues and manages digital certificates. Like a trusted notary public for the digital world.
- Registration Authority (RA): An intermediary that verifies the identity of certificate applicants before submitting their requests to the CA. They act as a filter, reducing the workload on the CA.
- Certificate Repository: A centralized location where certificates are stored and accessible. Think of it as a digital phone book for public keys.
- Digital Certificates: Electronic documents that bind a public key to the identity of an individual, organization, or other entity. They’re the proof of identity in the digital realm.
- Certificate Revocation List (CRL): A list of certificates that have been revoked due to compromise or other reasons. A kind of ‘wanted’ poster for invalid certificates.
- Online Certificate Status Protocol (OCSP): A real-time protocol for checking the validity of a certificate. A faster alternative to checking the CRL.
- Public Key Infrastructure (PKI) Management System: Software tools and processes for managing certificates, keys and other aspects of the PKI system.
These components work together to establish trust and secure communication across networks.
Q 2. Describe the process of certificate issuance and revocation.
The certificate issuance process involves several steps:
- Registration: The entity requesting a certificate (e.g., a website) submits an application to the RA or directly to the CA. This includes identity verification.
- Verification: The RA or CA verifies the applicant’s identity and ensures they have the right to request a certificate.
- Key Generation: The applicant generates a key pair (a public and a private key). The public key is included in the certificate.
- Certificate Signing Request (CSR): The applicant creates a CSR, which contains the public key and other relevant information.
- Certificate Issuance: The CA digitally signs the CSR, creating the certificate. This digital signature is what proves the CA’s endorsement.
- Distribution: The CA delivers the certificate to the applicant.
Certificate revocation is the process of declaring a certificate invalid. This is necessary if the private key is compromised or the information in the certificate is no longer accurate. This can be done through:
- Adding the certificate to the CRL: A batch process that might not be immediate.
- Using OCSP: Provides real-time verification status, negating the need to periodically consult the CRL.
Revocation ensures that compromised certificates are not used to impersonate or compromise systems.
Q 3. What are the different types of digital certificates?
There are various types of digital certificates, each serving a specific purpose:
- Domain Validation (DV) Certificates: The simplest type, verifying only ownership of a domain name. Commonly used for securing websites.
- Organization Validation (OV) Certificates: Verify both the domain name and the legal existence of the organization. Offers a higher level of trust than DV certificates.
- Extended Validation (EV) Certificates: The highest level of validation, involving extensive verification of the organization’s identity and legal status. EV certificates typically display the organization’s name in the browser’s address bar.
- Code Signing Certificates: Used to digitally sign software, ensuring its authenticity and integrity. It gives users confidence that the software hasn’t been tampered with.
- Email Certificates: Used for digitally signing and encrypting emails, ensuring authenticity and confidentiality of email communications. Think of them like digital signatures for email messages.
- Client Certificates: Used to authenticate users accessing network resources or applications. This adds extra security measures to access control.
The choice of certificate type depends on the security requirements and the level of trust needed.
Q 4. What is a Certificate Authority (CA) and what is its role in PKI?
A Certificate Authority (CA) is the cornerstone of a PKI. It’s a trusted third party that issues and manages digital certificates. Think of it as the ultimate authority that vouches for the authenticity of digital identities. Its role is crucial:
- Identity Verification: CAs rigorously verify the identity of certificate applicants to prevent fraud.
- Certificate Issuance: CAs generate and digitally sign certificates, binding public keys to identities.
- Certificate Revocation: CAs manage the revocation of certificates when necessary, ensuring compromised certificates are not used.
- Maintaining Trust: CAs maintain the trust chain by ensuring the security and integrity of their operations.
- Managing Certificate Lifecycle: CAs manage the entire lifecycle of certificates, from issuance to renewal to revocation.
The trust placed in a CA is paramount to the effectiveness of a PKI. Compromise of a CA can have devastating consequences, so their security practices are exceptionally stringent.
Q 5. Explain the concept of a Certificate Revocation List (CRL).
A Certificate Revocation List (CRL) is a published list of digital certificates that have been revoked by a CA. It’s essentially a list of ‘bad’ certificates that should no longer be trusted. It serves as a mechanism for identifying compromised certificates. Imagine it as a blacklist for digital identities.
CRLs are updated periodically. Checking a CRL to verify the validity of a certificate adds a layer of security, but it’s not instantaneous; there’s a delay between revocation and the update to the CRL. This delay can be a significant drawback in some situations.
Q 6. What is OCSP and how does it differ from CRL?
The Online Certificate Status Protocol (OCSP) is a real-time alternative to CRLs for checking the validity of certificates. Instead of consulting a periodically updated list, OCSP allows clients to directly query the CA (or an OCSP responder) to determine the current status of a certificate. Think of it as a live phone call to the authority instead of looking up a static list.
The main difference between OCSP and CRLs is the speed and efficiency. OCSP provides immediate responses about the certificate’s validity, whereas CRLs offer a delayed response.
However, OCSP introduces other considerations. It relies on the availability of the OCSP responder. If the responder is unavailable, certificate verification might fail.
Q 7. Describe the process of key generation and management in PKI.
Key generation and management are critical aspects of PKI. Secure key generation involves using strong algorithms and robust random number generators to produce a key pair – a public key and a private key. The public key can be shared freely, while the private key must be kept secret. Think of the public key as your address and the private key as your secret password.
Key management encompasses the entire lifecycle of keys, including:
- Generation: Using cryptographically secure techniques to create the keys.
- Storage: Securely storing private keys to protect them from unauthorized access. Often uses hardware security modules (HSMs) for enhanced security.
- Protection: Implementing access controls and security measures to prevent unauthorized access and use of keys.
- Rotation: Periodically replacing keys to mitigate risks associated with long-term key usage.
- Destruction: Securely destroying keys when they are no longer needed to prevent future compromise.
Poor key management practices are a major vulnerability in any PKI system. Robust key management is crucial to maintaining the integrity and security of the entire infrastructure.
Q 8. Explain the difference between symmetric and asymmetric encryption.
Symmetric and asymmetric encryption are two fundamental approaches to securing data, differing primarily in how they handle encryption keys.
Symmetric encryption uses the same secret key to encrypt and decrypt data. Imagine a padlock with one key; both the sender and receiver need this single key to lock (encrypt) and unlock (decrypt) the message. This is fast and efficient but presents a key distribution challenge: how do you securely share the secret key? Examples include AES (Advanced Encryption Standard) and DES (Data Encryption Standard).
Asymmetric encryption, on the other hand, uses a pair of keys: a public key and a private key. Think of a mailbox with a slot (public key) for anyone to drop in a letter (encrypted message), but only the owner possesses the key (private key) to open it and read the letter. The public key can be widely distributed, while the private key must remain secret. This elegantly solves the key distribution problem. RSA (Rivest-Shamir-Adleman) and ECC (Elliptic Curve Cryptography) are prominent examples.
In essence, symmetric encryption is like sharing a whisper, needing secrecy between the parties, while asymmetric encryption is like sending a postcard – anyone can see the address (public key), but only the recipient has the key to open it (private key).
Q 9. What are the security considerations when implementing PKI?
Implementing PKI securely requires careful consideration across several aspects:
- Key Management: This is paramount. Secure generation, storage, and rotation of private keys are crucial. Compromised private keys completely undermine the security of the entire system. Hardware Security Modules (HSMs) are often employed for enhanced protection.
- Certificate Authority (CA) Security: The CA is the cornerstone of PKI. Its security is paramount because it issues certificates. Any compromise of the CA would render the entire system vulnerable. Robust security measures for the CA infrastructure are essential, including physical security, intrusion detection, and rigorous access controls.
- Certificate Lifecycle Management: This involves establishing clear procedures for certificate issuance, renewal, revocation, and expiration. Automated systems are essential to manage large-scale certificate deployments efficiently and securely.
- Vulnerability Management: Regularly auditing PKI systems for vulnerabilities and promptly applying security patches to all components (servers, software, etc.) is a continuous process.
- Compliance and Auditing: Adhering to relevant industry standards and regulations (like PCI DSS, HIPAA, etc.) is critical. Regular audits help identify and rectify security weaknesses. Maintaining detailed logs of all PKI activities is also vital for forensic analysis.
Q 10. How does PKI ensure authentication and non-repudiation?
PKI ensures authentication and non-repudiation through digital certificates and digital signatures.
Authentication verifies the identity of a user or device. A digital certificate, issued by a trusted CA, binds a public key to an identity (e.g., a person’s name, a company’s domain). When you access a website using HTTPS, your browser checks the website’s certificate to verify its identity, ensuring you’re not communicating with an imposter.
Non-repudiation prevents users from denying they performed a specific action. Digital signatures use the sender’s private key to cryptographically sign a message, creating a digital fingerprint. Anyone with the sender’s public key can verify the signature, confirming the message’s authenticity and the sender’s identity. This ensures the sender cannot later deny having sent the message.
For example, consider an online banking transaction. The bank’s certificate authenticates the bank’s identity, and the user’s digital signature prevents them from denying the transaction.
Q 11. Explain the concept of digital signatures and their use in PKI.
A digital signature is a cryptographic technique used to verify the authenticity and integrity of data. It uses asymmetric cryptography to create a unique digital ‘fingerprint’ of a document or message.
In PKI, digital signatures are created by hashing the data (creating a fixed-size representation of the data) and then encrypting the hash with the sender’s private key. The recipient uses the sender’s public key to decrypt the hash and compare it to the hash of the received data. If the hashes match, the signature is verified; the data has not been tampered with, and it originated from the claimed sender.
Use in PKI: Digital signatures are extensively used for secure email, software distribution (ensuring software integrity), code signing, document signing (e.g., legally binding contracts), and secure transactions. They provide a mechanism for verifiable proof of origin and integrity in a digital world.
Q 12. What are the various algorithms used in PKI (e.g., RSA, ECC)?
PKI utilizes several cryptographic algorithms for key generation, encryption, and digital signatures. Some of the most common are:
- RSA (Rivest-Shamir-Adleman): A widely used asymmetric algorithm based on the difficulty of factoring large numbers. It’s used for both encryption and digital signatures.
- ECC (Elliptic Curve Cryptography): Another asymmetric algorithm that offers comparable security to RSA but with smaller key sizes, making it more efficient for resource-constrained devices like mobile phones and embedded systems.
- DSA (Digital Signature Algorithm): A digital signature algorithm that is primarily used for signing data, not encryption.
- AES (Advanced Encryption Standard): A symmetric algorithm that is highly efficient and widely used for encrypting data. It is often used alongside asymmetric algorithms in hybrid encryption schemes, where AES encrypts the data, and RSA or ECC encrypts the AES key.
The choice of algorithm often depends on security requirements, performance needs, and the specific application.
Q 13. Describe the role of hashing algorithms in PKI.
Hashing algorithms play a crucial role in PKI by providing a mechanism to create a unique fingerprint of data. A cryptographic hash function takes input data of any size and produces a fixed-size output, called a hash or message digest. Even a tiny change in the input data will result in a drastically different hash.
In PKI: Hashing is used in digital signatures to ensure data integrity. The data is hashed before signing, and the hash is signed instead of the entire data. This makes the process significantly more efficient. Upon verification, the recipient hashes the received data and compares it to the decrypted hash. If they match, it confirms the data’s integrity. Common hashing algorithms used in PKI include SHA-256 and SHA-384.
Q 14. How does PKI support secure communication over the internet?
PKI enables secure communication over the internet by providing a framework for authentication, confidentiality, and integrity.
HTTPS (HTTP Secure): This is the most prevalent example. Websites use SSL/TLS (Secure Sockets Layer/Transport Layer Security) protocols, which rely on PKI to establish a secure connection. The server presents its digital certificate to the client (browser), which verifies the certificate’s authenticity using the CA’s public key. Once authenticated, a secure, encrypted channel is established, protecting the communication between the client and the server.
Email Security (S/MIME): PKI underpins S/MIME (Secure/Multipurpose Internet Mail Extensions), enabling secure email communication through digital signatures and encryption. Digital signatures authenticate the sender and ensure message integrity, while encryption protects the message content from unauthorized access.
VPN (Virtual Private Network): PKI can be used in VPNs for authentication and secure key exchange, establishing a secure tunnel for communication over public networks.
In essence, PKI provides the digital trust infrastructure that forms the backbone of secure online communication.
Q 15. Explain the concept of certificate chaining.
Certificate chaining is like a chain of trust, verifying the authenticity of a digital certificate. Imagine you receive a letter with a signature. You might not know the signer personally, but if the letter is endorsed by someone you trust (like a notary), and that notary’s signature is further verified by a well-known authority, you’re more likely to accept its authenticity. Similarly, a certificate chain links a leaf certificate (the certificate you’re trying to verify) to a root certificate, which is self-signed and trusted by the system. Each certificate in the chain signs the certificate below it, building a chain of trust from the leaf to the root. If every signature in the chain is valid, the leaf certificate is deemed trustworthy.
For example, a website’s SSL certificate is a leaf certificate signed by a Certificate Authority (CA) like DigiCert or Let’s Encrypt. That CA’s certificate might in turn be signed by an intermediate CA, which is ultimately signed by the root CA. Your browser trusts the root CA, so by following the chain up to the root, it can verify the authenticity of the website’s certificate.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. What are the different types of certificate validation?
Certificate validation involves verifying the authenticity and integrity of a digital certificate. Several methods exist, each offering a different level of assurance:
- Basic Validation: This is a simple check of the certificate’s syntax and whether it’s signed by a trusted CA. It doesn’t verify the identity of the entity owning the certificate.
- Domain Validation (DV): This verifies that the certificate holder controls the domain name listed in the certificate. It’s usually achieved by proving ownership through email or DNS records. Think of this as verifying the address of the letter writer, not their identity.
- Organization Validation (OV): This goes further and verifies the legal existence and identity of the organization owning the certificate. It involves a more rigorous vetting process, providing a higher level of trust. It’s like checking the letter writer’s credentials beyond just their address.
- Extended Validation (EV): This is the highest level of validation. It involves a thorough examination of the organization’s identity and legal standing. EV certificates are often marked by a green bar in the browser’s address bar, clearly indicating a high level of trust. This is analogous to a letter signed and notarized by multiple highly reputable sources.
Q 17. What are some common vulnerabilities associated with PKI?
PKI systems, while providing crucial security, are vulnerable to various attacks. Some common vulnerabilities include:
- Compromised CA: If a Certificate Authority’s private key is compromised, attackers can issue fraudulent certificates, enabling them to impersonate legitimate entities. This would be akin to someone stealing the notary’s stamp.
- Certificate Revocation Issues: Ineffective certificate revocation procedures can allow compromised certificates to remain valid, leading to attacks. Think of it as continuing to accept mail from someone whose signature you’ve learned is forged.
- Weak Key Generation: Using weak or predictable cryptographic keys makes certificates vulnerable to brute-force or other attacks. Imagine using an easily guessable password to secure a very important document.
- Man-in-the-Middle Attacks: Attackers can intercept communication and issue their own fraudulent certificates, leading to data breaches. It’s like intercepting the letter and replacing it with a forgery.
- Phishing Attacks: Users can be tricked into installing malicious certificates or revealing sensitive information.
Q 18. How can you mitigate the risks associated with PKI?
Mitigating PKI risks requires a multi-layered approach:
- Choosing a Reputable CA: Selecting a well-established and trusted CA minimizes the risk of compromise.
- Regular Certificate Revocation: Implementing a robust certificate revocation system and promptly revoking compromised certificates is vital.
- Strong Key Management: Employing strong, randomly generated cryptographic keys and securing them properly is essential.
- Regular Security Audits: Periodic security assessments can identify vulnerabilities and weaknesses in the PKI infrastructure.
- Employee Training: Educating employees about phishing and social engineering attacks helps prevent human error.
- Use of Hardware Security Modules (HSMs): Storing private keys in HSMs provides a highly secure environment, protecting them from unauthorized access.
Q 19. Describe the process of deploying a PKI solution.
Deploying a PKI solution is a complex process involving careful planning and execution. It typically includes these steps:
- Needs Assessment: Define the scope of the PKI system, the entities to be included, and the security requirements.
- CA Selection: Choose a Certificate Authority (internal or external) based on your needs and budget.
- Infrastructure Setup: Set up the necessary infrastructure, including servers, databases, and network security.
- Certificate Generation: Generate certificates for each entity based on the defined roles and responsibilities.
- Deployment and Integration: Deploy the certificates to systems and applications and integrate them with existing security infrastructure.
- Testing and Validation: Thoroughly test the entire system to ensure its functionality and security before full deployment.
- Ongoing Management: Establish procedures for certificate renewal, revocation, and ongoing monitoring.
Q 20. What are some best practices for securing PKI certificates?
Securing PKI certificates requires diligent attention to several best practices:
- Strong Key Length: Use appropriately long keys (e.g., 2048-bit RSA or higher) to resist brute-force attacks.
- Regular Renewal: Renew certificates before they expire to maintain system security. A schedule for certificate renewals should be carefully planned and followed.
- Secure Storage: Protect private keys using HSMs or other secure storage solutions. Never leave private keys in plain text files.
- Use of OCSP Stapling: This allows servers to provide certificate revocation status efficiently, reducing reliance on external OCSP responders.
- Certificate Pinning: This involves hard-coding trusted certificate hashes in the client application, reducing the risk of MITM attacks.
- Regular Audits: Conduct regular security audits and penetration tests to identify vulnerabilities.
Q 21. How do you monitor and manage a PKI system?
Monitoring and managing a PKI system requires continuous vigilance. Key aspects include:
- Certificate Lifecycle Management: Track certificate expiration dates, renewal schedules, and revocation status.
- Log Monitoring: Regularly monitor audit logs to detect suspicious activity or security breaches.
- Security Auditing: Conduct periodic security audits to identify vulnerabilities and weaknesses.
- Revocation Monitoring: Regularly check the certificate revocation lists (CRLs) to ensure revoked certificates are properly handled.
- Performance Monitoring: Track the performance of the PKI system to identify and resolve any bottlenecks or issues.
- Alerting and Response: Implement alerts for critical events such as certificate expiration, revocation, or compromise, and establish response procedures for each event.
Q 22. Explain the importance of key escrow and recovery in PKI.
Key escrow and recovery in PKI are crucial mechanisms for managing the risk of key loss or compromise. Essentially, key escrow involves storing a copy of a private key in a secure location, accessible only under specific circumstances. Key recovery, on the other hand, refers to the process of retrieving this stored key when necessary. This is vital because without access to the private key, digital signatures can’t be verified, and encrypted data can’t be decrypted.
Imagine a scenario where a company’s encryption key is stored solely on a single employee’s laptop. If that employee leaves unexpectedly or the laptop is lost or stolen, access to critical data is lost, potentially causing significant financial or operational damage. Key escrow prevents this. A trusted third party, like a specialized key management service, holds a copy of the key. If the primary key is compromised or lost, the recovery process allows authorized personnel to retrieve the escrowed key, ensuring business continuity.
However, key escrow introduces security risks. The escrowed keys must be protected from unauthorized access. This usually involves stringent security measures, such as multi-factor authentication and robust encryption of the escrowed key. The balancing act is finding a solution that minimizes the risk of key compromise while still enabling data access if the primary key is unavailable.
Q 23. Describe your experience with specific PKI technologies (e.g., Microsoft CA, OpenSSL).
I’ve worked extensively with both Microsoft Certificate Authority (CA) and OpenSSL. With Microsoft CA, I’ve deployed and managed enterprise-level PKI solutions, configuring certificate templates, setting up certificate lifecycle management, and integrating with Active Directory. This involved hands-on experience with issuing various types of certificates like server authentication, client authentication, and code signing certificates. I’ve also troubleshooted certificate-related issues within Active Directory environments, including resolving certificate revocation list (CRL) distribution problems and addressing certificate renewal challenges.
My experience with OpenSSL is more focused on the command-line interface and scripting. I’ve used it to generate self-signed certificates for development and testing purposes and have also employed it for tasks like certificate verification and key management. OpenSSL’s flexibility and open-source nature are great for scripting automation around certificate operations, such as creating Certificate Signing Requests (CSRs) and verifying certificate chains.
In both cases, a deep understanding of certificate standards, like X.509, is paramount. I’ve successfully implemented best practices for secure key management and certificate storage, ensuring compliance with relevant industry regulations.
Q 24. How do you handle certificate expiration and renewal?
Certificate expiration and renewal are critical aspects of PKI management. To handle this effectively, I employ a proactive approach. First, a robust certificate inventory management system is essential. This involves regularly scanning for certificates nearing expiration, tracking their issuance date, and setting up alerts well before they expire. This allows sufficient time to plan for and execute the renewal process smoothly.
Automated renewal is highly desirable and can be achieved using various tools. With Microsoft CA, for instance, we can configure automatic certificate renewal policies. For self-signed certificates or certificates managed using tools like OpenSSL, we can create scripts to trigger the renewal process based on predefined criteria.
Prior to renewal, we should verify that the certificate’s associated private key is still secure and that the subject information is still accurate and updated. Finally, after a successful renewal, we must ensure the updated certificate is properly deployed and integrated into the relevant systems and applications.
Failure to manage certificate expiration can lead to security vulnerabilities and system outages. Imagine an SSL certificate expiring on a web server – the site would become inaccessible until the certificate is renewed, resulting in downtime and potential damage to the business’ reputation.
Q 25. What is the difference between self-signed and trusted certificates?
The core difference between self-signed and trusted certificates lies in their validation and trust level. A self-signed certificate is created and signed by the same entity, essentially acting as its own certificate authority. Think of it as someone signing their own school report card; you might believe it, but you lack independent verification of its authenticity.
Conversely, a trusted certificate is issued by a trusted certificate authority (CA), like DigiCert, Let’s Encrypt, or Comodo. These CAs are well-known and vetted, and their digital signatures are pre-installed in operating systems and browsers. The browser implicitly trusts these CAs, and hence, certificates signed by them are readily accepted without generating warnings. This is akin to a teacher signing the report card; the parent trusts the teacher’s verification.
Self-signed certificates are useful for internal development and testing environments where a high level of trust isn’t required. However, for production environments and external communications, trusted certificates are essential to establish trust and ensure secure communication.
Q 26. Explain how PKI is used in securing email communication (S/MIME).
PKI secures email communication using S/MIME (Secure/Multipurpose Internet Mail Extensions) by providing digital signatures and encryption for email messages. Digital signatures verify the sender’s identity and ensure message integrity, preventing forgery and tampering. This works by the sender digitally signing the email using their private key. The recipient then verifies the signature using the sender’s public key, confirming the sender’s identity and ensuring the message hasn’t been altered in transit.
Encryption, on the other hand, protects the confidentiality of the email content. The sender encrypts the message using the recipient’s public key, and only the recipient, with their private key, can decrypt and read the message. This safeguards sensitive information from unauthorized access.
Both digital signatures and encryption in S/MIME rely heavily on the secure management of public and private keys through the PKI system. The use of certificates issued by trusted CAs ensures that the recipient has confidence in the validity of the sender’s digital signature and the authenticity of the public key used for encryption.
Q 27. How does PKI contribute to secure web transactions (SSL/TLS)?
PKI plays a fundamental role in securing web transactions through SSL/TLS (Secure Sockets Layer/Transport Layer Security). SSL/TLS establishes a secure connection between a web browser and a web server, protecting sensitive data like credit card numbers, passwords, and personal information.
The server presents a digital certificate to the browser. This certificate contains the server’s public key and is signed by a trusted CA. The browser verifies the certificate’s authenticity and validity, checking its chain of trust back to a trusted root CA. This verification confirms the server’s identity and assures the browser that it is communicating with the legitimate entity.
Once the certificate is verified, a secure encrypted channel is established between the browser and server using the server’s public key. All subsequent communication between the browser and server is encrypted, preventing eavesdropping or tampering. The secure connection is indicated by the padlock icon in the browser’s address bar. Without PKI and its robust trust model, secure web transactions would be impractical and highly vulnerable.
Q 28. Discuss the role of PKI in securing IoT devices.
Securing IoT devices presents unique challenges, and PKI is a vital component in addressing these. IoT devices often have limited processing power and memory, so lightweight PKI solutions are crucial. This frequently involves employing smaller certificate sizes and using efficient cryptographic algorithms.
PKI enables secure communication between IoT devices and servers. Devices can be authenticated using certificates, ensuring only authorized devices can connect and communicate with the server. Furthermore, PKI ensures the integrity and confidentiality of the data exchanged between devices and servers, protecting sensitive data from unauthorized access and tampering. This is particularly important in applications where IoT devices handle sensitive information, such as medical sensors, smart home devices, or industrial control systems.
However, implementing PKI in IoT environments requires careful consideration of scalability and certificate lifecycle management, given the potentially large number of devices involved. Efficient certificate provisioning and revocation mechanisms are essential to address these scalability and management challenges, often requiring automated approaches.
Key Topics to Learn for Public-key infrastructure (PKI) Interview
- Core Concepts: Understand the fundamental principles of asymmetric cryptography, digital certificates, and certificate authorities (CAs).
- Certificate Lifecycle Management: Familiarize yourself with the processes involved in certificate generation, revocation, and renewal. Understand the role of CRLs and OCSP.
- Public Key Infrastructure Components: Learn about the different components of a PKI system, including registration authorities (RAs), certificate repositories, and directory services.
- Practical Applications: Explore real-world applications of PKI, such as secure email (S/MIME), website security (SSL/TLS), and code signing.
- Security Considerations: Understand potential vulnerabilities and attacks related to PKI, including certificate authority compromise and man-in-the-middle attacks.
- PKI Standards and Protocols: Become familiar with relevant standards like X.509 and protocols such as TLS/SSL.
- Troubleshooting and Problem Solving: Practice diagnosing common PKI-related issues and proposing solutions. Consider scenarios involving certificate errors, revocation issues, and key management problems.
- Hardware Security Modules (HSMs): Understand the role and importance of HSMs in securing private keys within a PKI system.
Next Steps
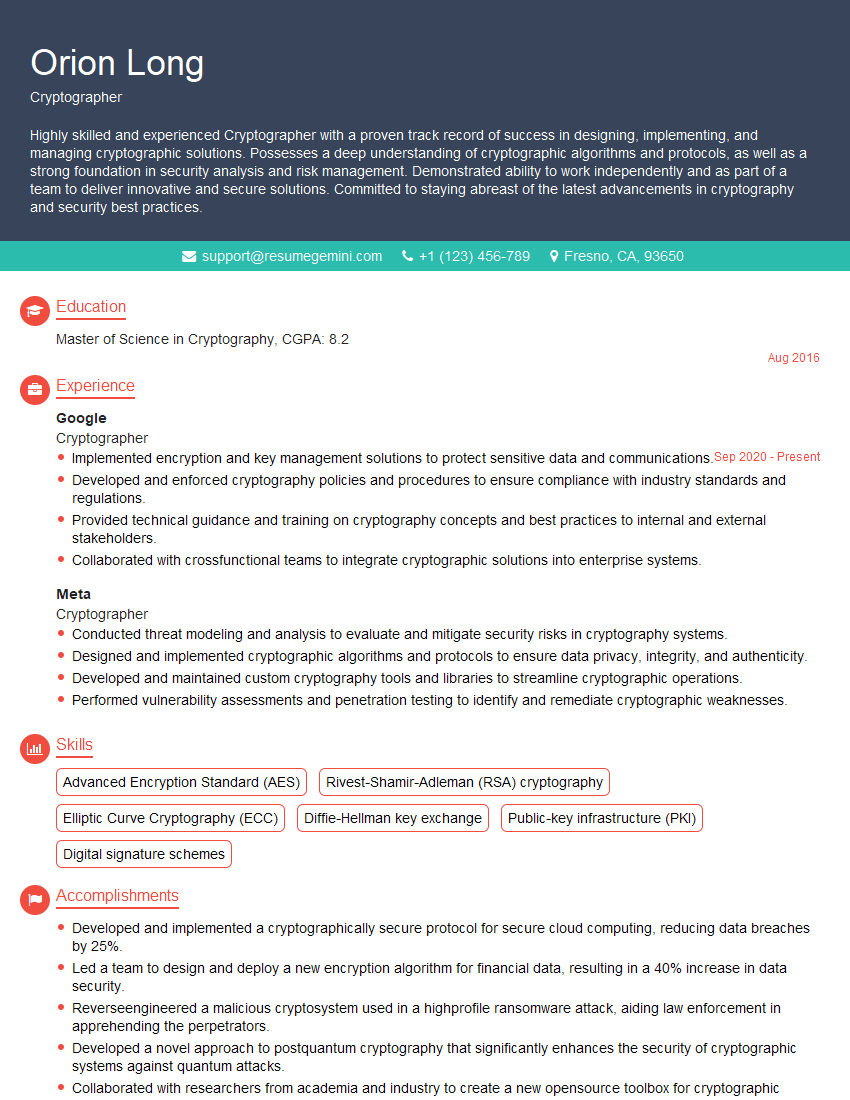
Mastering Public-key infrastructure (PKI) opens doors to exciting and high-demand roles in cybersecurity and IT. To maximize your job prospects, invest time in crafting an ATS-friendly resume that highlights your PKI expertise. ResumeGemini is a trusted resource to help you build a professional and impactful resume that showcases your skills effectively. We provide examples of resumes tailored to Public-key infrastructure (PKI) roles to guide you. Take the next step towards your dream career today!
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
I Redesigned Spongebob Squarepants and his main characters of my artwork.
https://www.deviantart.com/reimaginesponge/art/Redesigned-Spongebob-characters-1223583608
IT gave me an insight and words to use and be able to think of examples
Hi, I’m Jay, we have a few potential clients that are interested in your services, thought you might be a good fit. I’d love to talk about the details, when do you have time to talk?
Best,
Jay
Founder | CEO