Are you ready to stand out in your next interview? Understanding and preparing for Incident Escalation interview questions is a game-changer. In this blog, we’ve compiled key questions and expert advice to help you showcase your skills with confidence and precision. Let’s get started on your journey to acing the interview.
Questions Asked in Incident Escalation Interview
Q 1. Describe your experience with incident escalation procedures.
Incident escalation procedures are the formalized steps taken when a problem or incident exceeds the capabilities of the initial responder. My experience spans various industries and technologies, involving the escalation of incidents ranging from simple application errors to major service outages. I’ve worked within established escalation frameworks, like ITIL, and developed customized procedures for specific environments. This involves clearly defined roles and responsibilities, communication protocols, and escalation paths based on severity and impact.
For example, in my previous role, we used a tiered escalation system. Level 1 handled basic troubleshooting. Level 2 addressed more complex issues, involving specialized knowledge. Level 3 involved senior engineers and management for critical incidents impacting business operations. Each level had predefined escalation criteria and timelines.
- Understanding the incident: Thoroughly assessing the issue’s nature, scope, and impact before escalating.
- Following established procedures: Adhering to the defined escalation path and documentation requirements.
- Effective communication: Clearly conveying all relevant information to the next level of support.
Q 2. What metrics do you use to track incident escalation effectiveness?
Tracking the effectiveness of incident escalation relies on several key metrics. These metrics help identify areas for improvement and ensure the process is efficient and timely. Some crucial metrics include:
- Mean Time to Acknowledge (MTTA): How long it takes for the escalation to be acknowledged.
- Mean Time to Resolution (MTTR): The total time taken to resolve the incident after escalation.
- Escalation Frequency: The number of times incidents reach each level of support.
- Incident Severity Accuracy: How accurately incidents are initially classified, impacting the appropriate escalation.
- Customer Satisfaction (CSAT): Measuring customer happiness with the resolution process.
By analyzing these metrics, we can identify bottlenecks, improve response times, and refine escalation procedures for optimal performance. For instance, a high MTTR for a specific incident type might indicate a need for additional training or improved documentation for that area.
Q 3. Explain your process for determining the appropriate escalation path.
Determining the right escalation path involves a structured approach. It’s not simply about seniority; it’s about expertise and resource allocation. We consider several factors:
- Incident Severity: High-severity incidents (critical system failures, major security breaches) require immediate escalation to senior personnel.
- Incident Impact: The broader impact on business operations, users, or revenue.
- Technical Expertise: The specific skills needed to resolve the incident (e.g., database administration, network engineering).
- Resource Availability: Identifying the team or individual with the right skills and available time.
- Escalation Matrix: A predefined matrix mapping incident characteristics to escalation paths (often documented in a runbook or knowledge base).
Think of it like a medical triage system: the most critical cases receive immediate attention, while others are addressed according to their urgency and complexity.
Q 4. How do you ensure timely and efficient incident escalation?
Timely and efficient incident escalation is paramount. Several strategies ensure this:
- Automated Escalation Systems: Using monitoring tools and ticketing systems with automated escalation rules based on pre-defined criteria (e.g., alert thresholds, SLA breaches).
- Clear Communication Channels: Establishing readily available communication methods (e.g., dedicated phone lines, instant messaging, collaboration platforms) for prompt updates.
- Well-Defined Roles and Responsibilities: Knowing who is responsible for each escalation level minimizes confusion and delays.
- Regular Training and Drills: Ensuring all team members are familiar with escalation procedures and can respond effectively under pressure.
- Centralized Monitoring and Communication: Employing a central dashboard or system to track incidents and maintain visibility across all levels of escalation.
Proactive measures, like regular system checks and preventative maintenance, can significantly reduce the frequency of incidents requiring escalation.
Q 5. What communication methods do you use during an incident escalation?
Communication is key during escalation. We use a multi-faceted approach:
- Ticketing Systems: For formal documentation, tracking progress, and maintaining a record of communication.
- Instant Messaging: For quick updates and real-time collaboration between teams.
- Conference Calls: For involving multiple stakeholders and facilitating coordinated problem-solving.
- Email: For formal communication and longer updates.
- Status Reports: Regular updates to management and affected stakeholders on the incident’s progress.
Clear, concise, and factual communication is crucial to avoid confusion and ensure everyone is aligned on the situation and the response strategy. We use a standardized communication template to ensure consistency.
Q 6. How do you handle conflicting priorities during an incident escalation?
Conflicting priorities are inevitable. A structured approach is essential:
- Prioritization Matrix: Using a matrix that considers factors like severity, impact, and business criticality to prioritize incidents.
- Communication and Collaboration: Openly communicating conflicting priorities to all involved parties to find mutually agreeable solutions.
- Escalation to Management: If a resolution cannot be reached, escalating the conflict to management for decision-making.
- Temporary Workarounds: If needed, implementing temporary workarounds to mitigate the impact of less critical incidents while focusing on high-priority issues.
- Post-Incident Review: Analyzing the incident and identifying areas for process improvement to prevent similar conflicts in the future.
The goal is to balance all priorities effectively, minimizing disruption while addressing critical issues promptly.
Q 7. Describe a time you successfully escalated an incident.
During a major database outage impacting our e-commerce platform, initial troubleshooting by Level 1 support was unsuccessful. The system was unresponsive, and orders couldn’t be processed, resulting in significant financial losses and customer dissatisfaction. I immediately escalated the issue to Level 2, providing detailed logs and diagnostic data. Level 2 identified a critical configuration error. However, resolving this required expertise outside their domain.
I promptly escalated to Level 3, which included database administrators and senior engineers. We held a conference call involving all stakeholders, clearly outlining the problem, impact, and potential solutions. Level 3 specialists quickly diagnosed and rectified the issue, minimizing downtime. Post-incident review uncovered a lack of proper documentation for database configuration changes. We immediately addressed this gap to prevent similar occurrences.
This successful escalation highlighted the importance of clear communication, decisive action, and effective collaboration across different teams. It also demonstrated the value of a well-defined escalation process and a robust post-incident review procedure.
Q 8. Describe a time when an incident escalation failed. What did you learn?
One time, an escalation failed due to a lack of clear communication and a poorly defined escalation path. We were experiencing a significant database performance degradation affecting a critical customer-facing application. The initial team, lacking the specialized knowledge, tried several troubleshooting steps without success. Escalation to the database administrators happened too late, after significant downtime had already occurred. The information passed during the escalation was also insufficient, lacking key context such as recent database changes or error logs.
The key learning was the critical need for a well-defined escalation process with clear roles, responsibilities, and communication channels. We subsequently implemented a standardized escalation protocol, including mandatory runbooks and clearly defined escalation levels. We also invested in improved monitoring and alerting systems to provide real-time visibility into system health, enabling faster identification and escalation of critical issues. We also implemented better handover procedures, ensuring that critical information is consistently shared during escalations.
Q 9. How do you prioritize incidents for escalation?
Prioritizing incidents for escalation hinges on a combination of factors, prioritizing based on impact and urgency. We use a system that weighs these two factors using a simple matrix. Impact considers the number of users affected, the financial implications, and the potential reputational damage. Urgency looks at the time sensitivity – how quickly the issue needs to be resolved to minimize damage.
- High Impact, High Urgency: These incidents (e.g., complete system outage) are escalated immediately to the highest level.
- High Impact, Low Urgency: These incidents (e.g., slow database performance impacting many users) require immediate attention and swift escalation to the appropriate team for resolution.
- Low Impact, High Urgency: These incidents (e.g., a single user is unable to log in) may require a faster resolution, but escalation may not involve the highest levels of management.
- Low Impact, Low Urgency: These incidents (e.g., a minor UI bug affecting a few users) can often be handled by the initial support team without immediate escalation.
This matrix, coupled with clear Service Level Agreements (SLAs), provides a framework for consistent and effective prioritization. We also use automated tools to detect and flag incidents based on pre-defined thresholds, ensuring that critical events are immediately visible and prompt a timely escalation.
Q 10. How do you document incident escalations?
Detailed documentation is vital for effective incident management and continuous improvement. We use a centralized ticketing system to document every step of the escalation process. Each escalation record includes:
- Incident Summary: A concise description of the problem.
- Initial Response: Steps taken by the initial team.
- Escalation Timeline: The time each team was contacted and their response time.
- Escalation Path: The teams involved and their roles.
- Communication Log: A record of all communications (emails, phone calls, chat messages).
- Resolution Steps: The actions taken to resolve the incident.
- Root Cause Analysis (RCA): A detailed investigation into the underlying cause of the incident to prevent future occurrences.
- Post-Incident Review (PIR): An evaluation of the escalation process effectiveness identifying areas for improvement.
This detailed documentation allows for retrospective analysis, identifies trends, and facilitates knowledge sharing across teams. It is crucial for compliance, auditing purposes, and continuous process improvement.
Q 11. What tools or systems do you use to manage incident escalations?
We leverage a suite of tools to manage incident escalations effectively. Our primary system is a sophisticated ticketing system (e.g., ServiceNow, Jira Service Desk) which provides a centralized platform for incident tracking, escalation management, and communication. This integrates with our monitoring tools (e.g., Datadog, Prometheus) that provide real-time visibility into system health and trigger automated alerts based on predefined thresholds. This automated alerting helps trigger escalations quickly before issues become critical.
For communication during critical incidents, we use collaboration tools (e.g., Slack, Microsoft Teams) to facilitate real-time communication among the involved teams. We also utilize communication platforms to update stakeholders on progress and keep them informed about the resolution status.
Q 12. How do you involve stakeholders during an incident escalation?
Involving stakeholders effectively during an incident escalation is crucial for transparency and collaboration. We use a communication plan tailored to each stakeholder group. This plan identifies key communication channels and stakeholders’ preferred communication methods. Depending on the incident’s severity, we utilize different communication methods such as:
- Regular Updates: Providing timely updates through email, SMS, or our company’s communication portal.
- Dedicated Communication Channels: Creating dedicated channels (e.g., Slack channel, conference bridge) for real-time communication among stakeholders and the incident response team.
- Executive Briefings: Providing high-level summaries to senior management as needed.
- Transparency and Honesty: Providing clear and transparent communication, even if the situation is complex or uncertain, fostering trust and collaboration.
Keeping stakeholders informed is essential in minimizing uncertainty and maintaining trust. By adapting communication to the level of technical understanding of the stakeholders we ensure everyone is informed.
Q 13. How do you maintain clear communication during complex escalations?
Maintaining clear communication during complex escalations is paramount. We utilize several strategies to ensure consistent, accurate information dissemination:
- Centralized Communication Hub: Using a dedicated communication channel (e.g., Slack channel, shared document) to consolidate all information related to the escalation, preventing information silos.
- Designated Spokesperson: Appointing a single point of contact to ensure consistent messaging to all stakeholders.
- Regular Status Updates: Providing regular updates (e.g., hourly or as needed) to keep stakeholders informed of progress and any changes.
- Clear and Concise Messaging: Using plain language, avoiding technical jargon whenever possible, and delivering updates in a timely and concise manner.
- Documentation and Recording: Recording key decisions, actions, and communications to ensure transparency and facilitate post-incident review.
By focusing on these elements, we foster a culture of clear, open communication, promoting collaboration and improving the efficiency of incident resolution.
Q 14. How do you measure the impact of an incident escalation?
Measuring the impact of an incident escalation involves assessing both the immediate and long-term effects. We use Key Performance Indicators (KPIs) to track various aspects, including:
- Mean Time To Resolution (MTTR): How long it took to resolve the incident after escalation.
- Mean Time To Acknowledgement (MTTA): How quickly the escalated team acknowledged the incident.
- Downtime: The duration of service disruption caused by the incident.
- Financial Impact: The monetary loss due to the incident (e.g., lost revenue, customer churn).
- Customer Satisfaction: Feedback from affected customers on the handling of the incident.
- Effectiveness of RCA: How well the root cause analysis prevented recurrence of similar incidents.
By tracking these KPIs, we can identify areas for improvement in our escalation process and ensure that future escalations are more efficient and effective. Regular analysis of these metrics allows us to continually refine our processes and minimize the impact of future incidents.
Q 15. What are the key performance indicators (KPIs) you track for incident escalation?
Key Performance Indicators (KPIs) for incident escalation are crucial for measuring the effectiveness of our response and identifying areas for improvement. We track several key metrics, focusing on both speed and quality. These include:
- Mean Time To Acknowledge (MTTA): How quickly the escalation is acknowledged by the appropriate team. A high MTTA indicates potential bottlenecks in communication or resource availability.
- Mean Time To Resolution (MTTR): The average time it takes to completely resolve the incident after escalation. A high MTTR suggests inefficiencies in the escalation process or a lack of expertise within the responding team.
- Escalation Frequency: The number of incidents escalated within a given timeframe. A high frequency might point to underlying systemic issues requiring attention, such as insufficient training or inadequate monitoring.
- Incident Severity Classification Accuracy: This KPI measures how accurately incidents are initially classified, ensuring that appropriate resources are allocated promptly. Inaccurate classifications can lead to delayed resolutions.
- Customer Satisfaction (CSAT) related to escalation handling: This focuses on the customer’s experience during the escalation process. Were they kept informed? Were their needs addressed effectively? A low CSAT score highlights areas needing improvement in communication and service.
By regularly monitoring these KPIs, we can identify trends, pinpoint weaknesses, and proactively address issues within our escalation procedures, ultimately improving overall service reliability.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. Describe your approach to post-incident reviews related to escalations.
Post-incident reviews (PIRs) focusing on escalations are critical for continuous improvement. Our approach is structured and collaborative, involving all teams involved in the escalation. We follow these steps:
- Gather Data: We collect all relevant data, including logs, communication records, and any documentation from each team.
- Identify Root Cause: A thorough root cause analysis (RCA) is performed to understand why the incident escalated in the first place. This often involves using techniques like the ‘5 Whys’ to drill down to the underlying problem.
- Analyze Escalation Process: We examine every step of the escalation process, identifying bottlenecks, communication breakdowns, or areas where improvements can be made. For instance, were the right people contacted promptly? Was there enough information provided?
- Develop Actionable Recommendations: Based on the analysis, we develop specific, measurable, achievable, relevant, and time-bound (SMART) actions to prevent similar escalations in the future. This might include updating procedures, improving training, or investing in new monitoring tools.
- Implement and Monitor: The agreed-upon actions are implemented, and their effectiveness is monitored using the KPIs mentioned earlier. We revisit the PIR findings at regular intervals to assess progress.
For example, if an escalation took longer than expected due to a lack of expertise, we might add specialized training for the relevant team or update our escalation matrix to involve the appropriate expert from the start.
Q 17. How do you manage escalations involving multiple teams or departments?
Managing escalations involving multiple teams or departments requires a structured approach and strong communication. We utilize a centralized escalation management system, often a ticketing system with clear roles and responsibilities defined for each team. This system allows for:
- Clear Communication Channels: A dedicated communication channel ensures all involved parties are kept informed and can easily share updates.
- Centralized Information Repository: The system acts as a central repository for all relevant information, preventing information silos and ensuring everyone is on the same page.
- Role-Based Access Control: Access control ensures that only authorized personnel can view and modify sensitive information.
- Defined Escalation Paths: Clearly defined escalation paths ensure that the incident is routed efficiently to the correct team and individuals based on their expertise and availability.
- Regular Status Meetings: Regular status meetings help to track progress and identify any roadblocks or conflicts.
Imagine a network outage affecting multiple applications. The escalation will involve the network team, application teams, and potentially the security team. The centralized system enables all these teams to collaborate effectively, track progress, and resolve the issue faster.
Q 18. How do you handle escalations outside of normal business hours?
Handling escalations outside of normal business hours requires a robust on-call rotation and a clear escalation procedure. We have clearly defined on-call schedules for each team and an escalation matrix that specifies who to contact depending on the severity of the incident. We utilize tools such as:
- On-call scheduling software: This software automates the on-call rotation, sending notifications to the appropriate personnel.
- Automated alerting systems: Automated systems trigger alerts when critical incidents occur, ensuring that the on-call team is notified immediately.
- Dedicated communication channels: Secure and readily accessible communication channels, such as dedicated phone lines or messaging platforms, are used for out-of-hours communication.
- Detailed documentation: Comprehensive documentation, including troubleshooting guides and runbooks, allows the on-call team to quickly diagnose and resolve incidents.
We also ensure regular training and drills for the on-call team to maintain their readiness and proficiency in handling out-of-hours escalations. This ensures a swift response even outside of regular business hours, minimizing disruption and downtime.
Q 19. How familiar are you with ITIL frameworks and their application to incident escalation?
I am very familiar with ITIL (Information Technology Infrastructure Library) frameworks and their application to incident escalation. ITIL provides a structured approach to IT service management, and its principles are highly relevant to effective escalation management. Specifically:
- Incident Management: ITIL’s incident management process provides a framework for identifying, classifying, and resolving incidents. Escalation is a key part of this process, ensuring that incidents are handled by the appropriate personnel with the necessary expertise.
- Problem Management: ITIL emphasizes identifying and resolving the underlying causes of incidents (problems) to prevent recurrence. This is closely tied to post-incident reviews, a crucial aspect of effective escalation management.
- Change Management: ITIL’s change management process helps to minimize the risk of incidents arising from changes to the IT infrastructure. This reduces the need for escalations by preventing disruptions in the first place.
- Service Level Management: ITIL’s service level management process defines service level agreements (SLAs) that dictate the expected response times and resolution times for incidents. These SLAs are crucial for determining when and how an incident should be escalated.
Understanding and applying ITIL principles significantly enhances the efficiency and effectiveness of our incident escalation procedures.
Q 20. How do you ensure that escalations are documented accurately and completely?
Accurate and complete documentation of escalations is paramount for accountability, analysis, and continuous improvement. We ensure this through:
- Centralized Ticketing System: All escalations are logged in a centralized ticketing system, ensuring a single source of truth for all incident-related information.
- Structured Templates: We use structured templates for recording escalation details, including timestamps, involved parties, actions taken, and outcomes. This ensures consistency and completeness.
- Mandatory Fields: The ticketing system includes mandatory fields to capture critical information such as incident severity, root cause, and resolution steps.
- Regular Audits: Regular audits of the ticketing system help to identify gaps in documentation and ensure that procedures are being followed consistently.
- Automated Notifications: Automated notifications remind personnel to update the ticket with relevant information at key stages of the escalation process.
This comprehensive documentation enables us to analyze trends, identify areas for improvement, and ultimately deliver better service to our users. Incomplete documentation hinders effective analysis and improvement efforts.
Q 21. What are some common challenges you face during incident escalations?
Common challenges encountered during incident escalations include:
- Communication Barriers: Ineffective communication between teams or individuals can significantly delay resolution. This can be due to unclear escalation paths, lack of available personnel, or simply poor communication skills.
- Lack of Information: Insufficient information provided during the initial escalation can hinder the ability of the receiving team to quickly diagnose and resolve the issue. This necessitates back-and-forth communication, delaying the resolution process.
- Unclear Responsibilities: Ambiguity regarding roles and responsibilities can lead to confusion and delays. Clearly defined escalation paths and roles are essential to avoid this.
- Insufficient Resources: Lack of sufficient personnel, tools, or expertise can impede the ability of the responding team to effectively address the incident.
- Resistance to Change: Resistance to adopting new procedures or technologies can also hinder improvements in the escalation process.
Overcoming these challenges requires proactive measures, such as improving communication channels, providing comprehensive training, investing in appropriate tools, and fostering a culture of continuous improvement.
Q 22. How do you ensure that critical incidents are addressed immediately?
Ensuring immediate attention to critical incidents hinges on a robust escalation process and proactive monitoring. It’s not just about reacting quickly; it’s about being prepared. We achieve this through a multi-pronged approach:
- Real-time Monitoring: We leverage monitoring tools that provide alerts based on predefined thresholds. For example, a significant drop in website traffic or a spike in error logs would trigger an immediate alert. This proactive approach prevents issues from escalating beyond a manageable level.
- Clearly Defined Escalation Paths: We have well-documented escalation paths outlining who to contact, what information to provide, and the expected response time for each severity level (critical, major, minor). This ensures that the right people are notified promptly and efficiently.
- On-Call Rotation: A dedicated, skilled on-call team ensures 24/7 coverage. Members are equipped with the necessary tools and knowledge to quickly assess and respond to critical incidents. Regular training and drills keep them sharp and prepared.
- Automated Response Systems: Where possible, we use automated systems to initiate initial responses such as restarting services or rerouting traffic. This buys valuable time and minimizes the impact of the incident.
Imagine a scenario where our primary database becomes unavailable. Our monitoring system would immediately trigger alerts to the on-call database administrator and the incident management team. The automated system might attempt to restart the database. Concurrently, the on-call team would initiate the established escalation path, informing relevant stakeholders and working on a resolution.
Q 23. How do you identify and resolve recurring incidents that require escalation?
Identifying and resolving recurring incidents requires a systematic approach that goes beyond simply fixing the immediate problem. It necessitates root cause analysis and proactive measures. We utilize the following strategies:
- Incident Tracking and Analysis: We meticulously document every incident, including its symptoms, resolution steps, and root cause. We use tools to track recurring issues, identifying patterns and trends.
- Root Cause Analysis (RCA): For recurring incidents, we conduct thorough RCA sessions involving relevant stakeholders. The ‘5 Whys’ technique, for example, is helpful in drilling down to the underlying cause. This helps us understand ‘why’ the incident occurred, not just ‘what’ happened.
- Knowledge Base Updates: Once the root cause is identified and a solution implemented, we update our internal knowledge base with the details. This ensures that future incidents of the same nature are easily resolved, preventing escalation.
- Automated Remediation: In some cases, we can automate remediation steps to prevent the recurrence of a problem. For instance, a recurring script error might be addressed through automated code deployment with stricter testing procedures.
For example, if we experience repeated login failures due to a specific user input validation issue, RCA would reveal the faulty validation code. Updating the code and adding rigorous testing would prevent future escalations of this issue.
Q 24. What strategies do you use to prevent future incidents from requiring escalation?
Preventing future escalations is a proactive endeavor focused on improving system reliability, enhancing operational processes, and empowering staff. We employ these strategies:
- Proactive Monitoring and Alerting: Robust monitoring ensures early detection of potential problems before they escalate. This includes setting appropriate thresholds and regularly reviewing alert configurations.
- Regular System Maintenance: Scheduling preventative maintenance, such as software updates and hardware checks, minimizes the risk of unexpected outages and errors.
- Comprehensive Training and Documentation: Well-trained staff are less likely to cause incidents. Clear, up-to-date documentation ensures consistent processes and simplifies troubleshooting.
- Capacity Planning: Predicting future demand and scaling infrastructure accordingly ensures the system can handle peak loads without performance degradation.
- Security Audits and Penetration Testing: Regular security assessments identify vulnerabilities that could be exploited, reducing the likelihood of security-related escalations.
Think of it like car maintenance. Regular oil changes, tire rotations, and inspections prevent major breakdowns. Similarly, proactive measures prevent IT incidents from escalating into crises.
Q 25. Explain your understanding of the concept of escalation fatigue.
Escalation fatigue is a state of exhaustion and demoralization experienced by individuals frequently involved in incident handling, particularly when issues are repetitive, unresolved, or poorly communicated. It’s the feeling of being constantly ‘on call’ with little relief. This can lead to burnout, reduced responsiveness, and increased error rates.
Imagine a team constantly dealing with the same network connectivity issue due to a poorly configured router. The repeated escalations, coupled with the lack of permanent solution, would lead to exhaustion and a sense of helplessness amongst the team, creating escalation fatigue. It’s crucial to acknowledge this and implement solutions to prevent it.
Q 26. How do you handle pressure and stress during a critical incident escalation?
Handling pressure during a critical incident requires a calm, structured approach. My strategy relies on these key elements:
- Deep Breaths and Focused Attention: Taking a moment to breathe deeply helps regulate my stress response, allowing for clearer thinking under pressure.
- Structured Problem Solving: Focusing on the problem-solving process, using established frameworks (e.g., incident management lifecycle), rather than emotional reactions helps maintain control.
- Clear Communication: Keeping stakeholders informed and transparent about the situation and progress reduces anxiety and builds trust.
- Seeking Support: Not being afraid to ask for help from colleagues or supervisors ensures a shared burden and prevents individual burnout.
- Post-Incident Debrief: A structured debrief allows for reflection, identifying areas for improvement, and reducing the likelihood of future stressful situations.
In a high-pressure situation, maintaining composure is paramount. A calm demeanor reassures the team and promotes effective collaboration in resolving the crisis.
Q 27. How do you delegate tasks effectively during an incident escalation?
Effective delegation during an incident escalation requires clear communication, defined roles, and trust in team members’ abilities. My approach involves:
- Assessing Team Member Skills: I delegate tasks based on each team member’s expertise and available resources.
- Clearly Defined Tasks and Expectations: Each delegated task includes specific instructions, timelines, and expected outcomes. This minimizes ambiguity and ensures everyone understands their role.
- Regular Communication and Updates: Maintaining open communication channels allows for real-time updates and addresses any questions or challenges that arise.
- Empowerment and Trust: I empower team members to make decisions within their area of responsibility, fostering ownership and accountability.
- Monitoring and Support: I monitor progress and offer support when needed, ensuring tasks are completed efficiently and effectively.
For instance, during a server outage, I might delegate the task of communicating with affected users to a communication specialist while assigning the technical diagnosis to the server administrator.
Q 28. What are some strategies for reducing the number of incident escalations?
Reducing incident escalations requires a holistic approach that combines proactive measures with reactive improvements. The key strategies include:
- Improved Monitoring and Alerting: Implementing comprehensive monitoring systems with intelligent alerts can detect problems early, preventing escalation.
- Strengthened Root Cause Analysis: Thorough RCA and implementation of corrective actions prevent recurring incidents.
- Enhanced Training and Documentation: Well-trained staff with access to comprehensive documentation are less prone to errors.
- Automation: Automating repetitive tasks reduces human error and frees up resources for more complex issues.
- Proactive Capacity Planning: Ensuring sufficient infrastructure capacity prevents performance issues.
- Regular Security Assessments: Identifying and mitigating security vulnerabilities reduces the risk of security breaches.
- Continuous Improvement: Regularly reviewing incident reports and feedback helps identify areas for improvement in processes and technologies.
By focusing on prevention and continuous improvement, we can create a more resilient and stable system, minimizing the need for incident escalations.
Key Topics to Learn for Incident Escalation Interview
- Understanding Incident Severity and Urgency: Learn to differentiate between severity (impact) and urgency (time sensitivity) and apply this knowledge to prioritize escalations effectively.
- Effective Communication Strategies: Practice concise and clear communication techniques, including verbal and written updates, ensuring stakeholders receive timely and relevant information. Consider the different communication styles needed for various stakeholders (technical vs. non-technical).
- Incident Management Frameworks (ITIL, etc.): Familiarize yourself with common frameworks and their application in the escalation process. Understand the roles and responsibilities involved in each stage.
- Root Cause Analysis (RCA): Learn different RCA methodologies and how to apply them to identify the underlying cause of incidents, preventing future recurrences. Practice articulating your RCA approach and findings.
- Escalation Paths and Procedures: Understand the established escalation paths within an organization and how to navigate them efficiently and effectively, adhering to company protocols and Service Level Agreements (SLAs).
- Documentation and Reporting: Master the art of detailed and accurate documentation of incidents, including steps taken, outcomes, and lessons learned. Practice presenting this information clearly and concisely.
- Stakeholder Management: Develop strategies for effectively managing expectations and communications with diverse stakeholders during an incident, ensuring transparency and collaboration.
- Problem Solving and Decision Making Under Pressure: Practice critical thinking and problem-solving skills in simulated high-pressure situations, showcasing your ability to remain calm and make informed decisions.
Next Steps
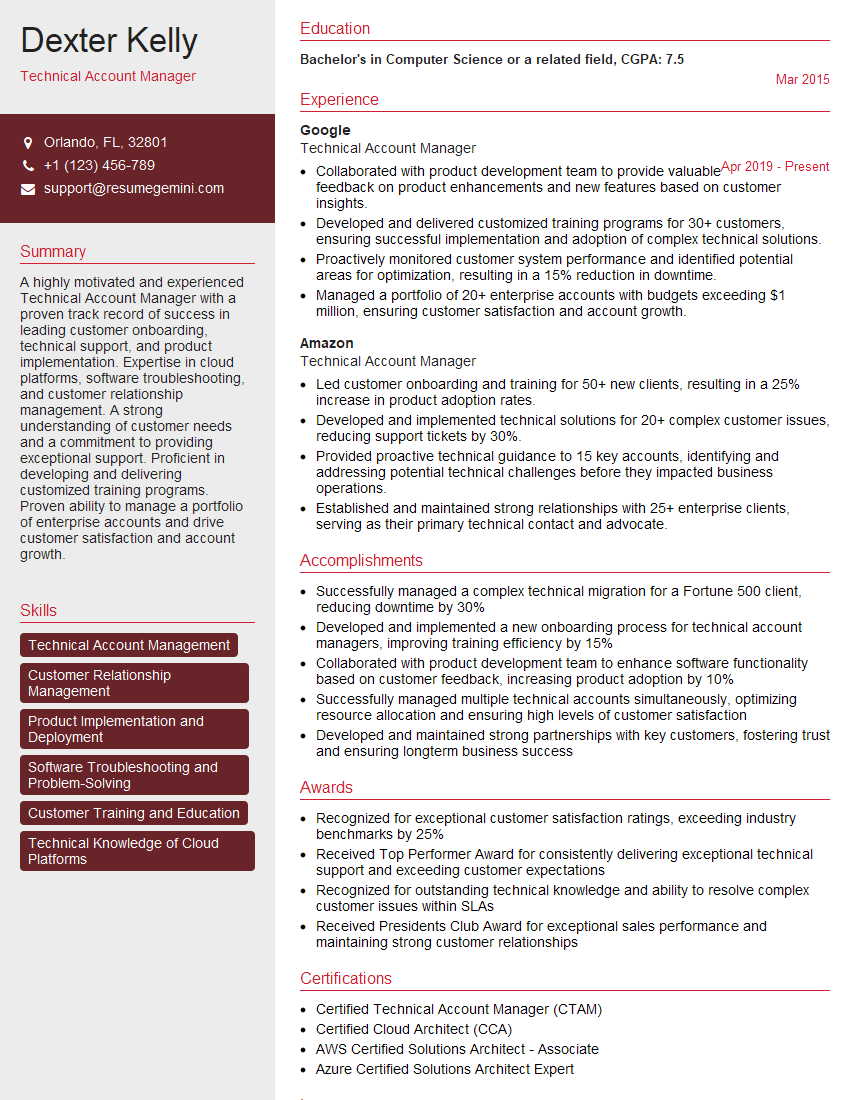
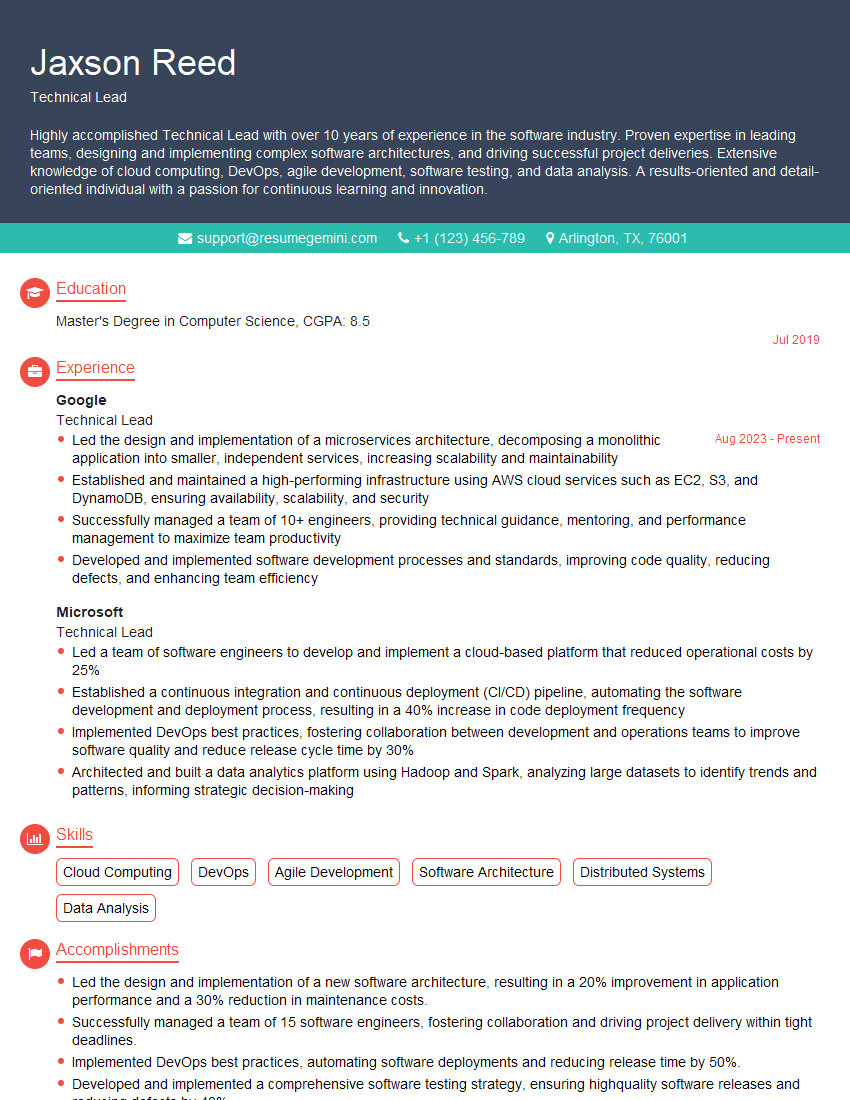
Mastering incident escalation is crucial for career advancement in IT and related fields. It demonstrates your ability to handle pressure, solve complex problems, and collaborate effectively within a team. To maximize your job prospects, creating a strong, ATS-friendly resume is essential. ResumeGemini is a trusted resource to help you build a professional and impactful resume tailored to your skills and experience. Examples of resumes specifically tailored for Incident Escalation roles are available to guide you through the process.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Really detailed insights and content, thank you for writing this detailed article.
IT gave me an insight and words to use and be able to think of examples