Are you ready to stand out in your next interview? Understanding and preparing for Advanced Radio Communication interview questions is a game-changer. In this blog, we’ve compiled key questions and expert advice to help you showcase your skills with confidence and precision. Let’s get started on your journey to acing the interview.
Questions Asked in Advanced Radio Communication Interview
Q 1. Explain the concept of frequency hopping spread spectrum.
Frequency Hopping Spread Spectrum (FHSS) is a spread-spectrum technique that transmits data across multiple frequencies, hopping between them according to a pseudorandom sequence known only to the transmitter and receiver. Imagine a conversation happening across many different radio channels, constantly switching to avoid eavesdropping or interference. This hopping pattern makes it difficult for unintended recipients to decipher the message because they don’t know the frequency hopping sequence. The advantage lies in its robustness against jamming and interference – if an adversary jams one frequency, the communication simply hops to another. It’s also useful for secure communication as interception requires knowledge of the hopping sequence.
For example, Bluetooth uses FHSS to allow multiple devices to communicate simultaneously without interfering with each other. Each device uses a unique hopping sequence, preventing collisions. The pseudorandom nature of the hopping pattern ensures unpredictability, adding to security.
Q 2. Describe the differences between OFDM and OFDMA.
Both Orthogonal Frequency Division Multiplexing (OFDM) and Orthogonal Frequency Division Multiple Access (OFDMA) are modulation techniques that divide a high-bandwidth channel into many smaller, orthogonal subcarriers. Think of it like splitting a wide river into many smaller, parallel streams. The key difference lies in how they utilize these subcarriers.
OFDM uses all subcarriers for a single user’s transmission, maximizing the bandwidth for that user. OFDMA, however, allows multiple users to share the subcarriers simultaneously. Each user is assigned a subset of subcarriers. This is like allocating specific stream segments of the river to individual boats instead of giving the entire river to a single boat. OFDMA is therefore more efficient in supporting multiple users compared to OFDM, making it ideal for cellular networks like 4G LTE and 5G NR.
Q 3. What are the challenges associated with implementing MIMO in a real-world scenario?
Multiple-Input Multiple-Output (MIMO) technology uses multiple antennas at both the transmitter and receiver to increase data rates and improve link reliability. However, real-world implementation faces several challenges:
- Channel Estimation: Accurately estimating the channel characteristics between each antenna pair is crucial. Imperfect channel estimation leads to performance degradation.
- Antenna Spacing: Sufficient spacing between antennas is necessary to ensure the signals are relatively independent. In compact devices, this can be difficult to achieve.
- Hardware Complexity: MIMO systems require more complex hardware, leading to higher costs and power consumption.
- Calibration and Synchronization: Maintaining accurate calibration and synchronization between multiple antennas is essential. Any drift or mismatch can severely impact performance.
- Propagation Effects: Multipath fading and shadowing can affect the performance of MIMO systems. Mitigation techniques are needed to address these issues.
For instance, in a dense urban environment, the reflections from buildings create significant multipath fading which MIMO must compensate for. This requires sophisticated signal processing algorithms to mitigate these effects.
Q 4. How do you mitigate multipath fading in wireless communication systems?
Multipath fading occurs when the transmitted signal arrives at the receiver via multiple paths, causing constructive and destructive interference. This leads to signal fluctuations and potential loss of data. Several techniques mitigate multipath fading:
- Equalization: Adaptive equalization techniques analyze the received signal and compensate for the distortions caused by multipath. This is analogous to adjusting the sound level of individual instruments in an orchestra to achieve a balanced sound.
- Diversity Techniques: Employing multiple antennas (spatial diversity), using different frequencies (frequency diversity), or transmitting the same signal multiple times with different time delays (time diversity) can help to mitigate the effects of fading. Having multiple copies of the signal statistically increases the chance of at least one being strong.
- Coding Techniques: Forward error correction (FEC) codes add redundancy to the transmitted data, allowing the receiver to correct errors introduced by multipath fading. This is akin to sending duplicate copies of an important document.
- Interleaving: Data is rearranged before transmission and rearranged again at the receiver. This spreads out the impact of bursts of errors caused by multipath fading.
Q 5. Explain the principles of adaptive antenna arrays.
Adaptive antenna arrays employ multiple antennas that can dynamically adjust their radiation patterns based on the channel conditions. Imagine a spotlight that can automatically focus on a specific target, ignoring distractions. This improves signal reception and reduces interference.
The principles involve using signal processing techniques to determine the direction of arrival (DoA) of signals, and then adjusting the phase and amplitude of each antenna element to create a desired beam pattern. This can be achieved through algorithms like Minimum Mean Squared Error (MMSE) or Maximum Ratio Combining (MRC). By steering the beam towards the desired signal and nulling out interference, the signal-to-noise ratio (SNR) is improved, leading to enhanced performance and better link quality. For example, in cellular base stations, adaptive antenna arrays are used to focus the signal towards mobile devices, improving coverage and capacity.
Q 6. Describe the different types of modulation techniques used in advanced radio communication.
Advanced radio communication employs various modulation techniques, each with its strengths and weaknesses. The choice depends on factors such as bandwidth efficiency, power efficiency, and robustness to noise and fading.
- Amplitude Shift Keying (ASK): Information is encoded by varying the amplitude of the carrier wave. Simple but susceptible to noise.
- Frequency Shift Keying (FSK): Information is encoded by varying the frequency of the carrier wave. More robust to noise than ASK.
- Phase Shift Keying (PSK): Information is encoded by varying the phase of the carrier wave. Offers higher bandwidth efficiency compared to ASK and FSK.
- Quadrature Amplitude Modulation (QAM): Combines both amplitude and phase modulation. Achieves high bandwidth efficiency but is more sensitive to noise.
- Orthogonal Frequency Division Multiplexing (OFDM): As discussed previously, divides the channel into multiple orthogonal subcarriers, improving robustness to multipath fading.
For example, WiFi typically uses OFDM for its high bandwidth efficiency, while some low-power devices might employ FSK for its simplicity and low power consumption.
Q 7. What are the advantages and disadvantages of using different antenna types (e.g., dipole, patch, horn)?
Different antenna types offer trade-offs in terms of gain, bandwidth, size, and cost.
- Dipole Antennas: Simple, inexpensive, and relatively easy to manufacture. They offer moderate gain and bandwidth. A classic example is the TV antenna.
- Patch Antennas: Compact, low-profile antennas suitable for integration into devices. They offer moderate gain and bandwidth, making them popular in mobile devices.
- Horn Antennas: Provide high gain and directivity, making them suitable for applications requiring long-range communication or focusing the signal in a specific direction. Often used in satellite communication systems.
For example, a mobile phone would use a patch antenna due to its small size and moderate performance requirements. A satellite ground station, on the other hand, may use a horn antenna to achieve high gain and focused transmission towards the satellite.
The selection depends on the specific application requirements. Considerations include operating frequency, desired gain, size constraints, and cost limitations.
Q 8. Explain the concept of channel equalization.
Channel equalization is a crucial technique in advanced radio communication used to compensate for the distorting effects of the communication channel. Think of it like this: you’re trying to send a perfectly clear voice message across a noisy room. The room acts as the channel, introducing echoes, reverberations, and other distortions that muddle your message. Channel equalization is like having a sophisticated noise-canceling microphone that filters out the unwanted distortions, allowing the recipient to hear your voice clearly.
In technical terms, the channel introduces frequency-dependent attenuation and phase shifts to the transmitted signal. Equalization uses a filter, often an adaptive filter (meaning it adjusts its characteristics based on the channel’s current state), to counteract these effects. This filter’s design is based on estimating the channel’s impulse response, which is a characterization of how the channel affects the signal in the time domain. Popular equalization techniques include linear equalization (e.g., zero-forcing, minimum mean-squared error), decision-feedback equalization, and more advanced methods like maximum likelihood sequence estimation (MLSE) for complex channels. The choice of method depends heavily on the channel characteristics and computational constraints.
For instance, in high-speed digital subscriber lines (DSL) technology, channel equalization is vital to mitigate the distortions introduced by the twisted-pair copper wires, enabling high data rates over these relatively low-quality channels. Similarly, in wireless communication, equalization combats the effects of multipath propagation (where the signal takes multiple paths to the receiver, causing delays and interference).
Q 9. How do you perform link budget analysis for a wireless communication system?
Link budget analysis is a critical step in designing any wireless communication system. It’s essentially a careful accounting of all the power gains and losses involved in transmitting and receiving a signal. The goal is to ensure the received signal strength is sufficient for reliable communication. Imagine shining a flashlight across a field – you need enough light intensity at the receiver to see it clearly. Link budget analysis helps determine if your ‘flashlight’ (transmitter) is powerful enough and the conditions (obstacles, atmospheric interference, etc.) are favorable enough for the receiver to ‘see’ the signal.
The analysis involves calculating the transmit power, antenna gains, path losses (due to distance, atmospheric attenuation, etc.), and receiver noise figure. The process typically involves the following steps:
- Calculate Transmit Power (Pt): This includes the power output of the transmitter and any antenna gains.
- Determine Path Loss (Lp): This is usually calculated using a path loss model appropriate for the propagation environment (e.g., free space path loss, Okumura-Hata model, etc.). It accounts for signal attenuation due to distance and other environmental factors.
- Account for other losses (Lother): This could include cable losses, atmospheric absorption, and fading effects.
- Calculate Receiver Noise Figure (NF): This quantifies the noise added by the receiver.
- Calculate Receiver Sensitivity (Pr): This is the minimum power needed at the receiver for acceptable performance.
The link budget equation is typically expressed as: Pr ≥ Pt + Gt + Gr – Lp – Lother – NF. Where Gt and Gr are transmitter and receiver antenna gains, respectively. If the calculated received power (Pr) is greater than or equal to the receiver sensitivity, the link is considered viable. Otherwise, adjustments need to be made, possibly involving increasing transmit power, using higher-gain antennas, or reducing interference.
Q 10. What are the key performance indicators (KPIs) for a wireless communication system?
Key Performance Indicators (KPIs) for a wireless communication system are metrics used to assess its performance and reliability. Different KPIs are relevant based on the specific application, but some common ones include:
- Throughput: The rate at which data is successfully transmitted, often measured in bits per second (bps) or megabits per second (Mbps).
- Latency: The time delay experienced from signal transmission to reception, crucial for real-time applications.
- Bit Error Rate (BER): The percentage of bits that are received incorrectly, indicating the reliability of the communication link. A lower BER is better.
- Packet Loss Rate: The percentage of data packets that are lost during transmission, another measure of reliability.
- Signal-to-Interference-plus-Noise Ratio (SINR): The ratio of the desired signal power to the sum of interference and noise power. A higher SINR generally indicates better performance.
- Availability: The percentage of time the system is operational and available for use.
- Coverage Area: The geographical area within which the system provides acceptable signal strength and quality.
Monitoring these KPIs allows engineers to identify potential problems, optimize system parameters, and ensure the system meets the required performance specifications. For example, a high packet loss rate might indicate problems with the channel, while a low throughput might suggest limitations in the modulation scheme or network capacity.
Q 11. Explain the concept of interference cancellation.
Interference cancellation is a technique to mitigate the effects of unwanted signals (interference) on a desired signal. Imagine trying to have a conversation in a crowded room – many other voices interfere with your ability to understand the person you are talking to. Interference cancellation is like having a sophisticated system that filters out all those other voices, leaving only the voice you wish to hear.
Several methods exist for interference cancellation. One common approach is using adaptive filters. The filter estimates the characteristics of the interference and generates a signal to subtract it from the received signal, effectively canceling it out. The success of this depends on having some knowledge of the interference’s properties (or at least the ability to estimate them). Another method, common in multi-antenna systems (MIMO), leverages spatial filtering techniques to separate the desired signal from interfering signals based on their different angles of arrival. Space-time processing combines spatial and temporal filtering for superior interference rejection.
For example, in cellular networks, interference cancellation techniques are vital to mitigate interference from neighboring base stations operating on the same or adjacent frequency bands. This ensures each user can receive a relatively clean signal and achieve high data rates. Similarly, in cognitive radio systems, advanced interference cancellation techniques are crucial to allow secondary users to access unused spectrum without harming primary users’ operation.
Q 12. Describe different methods for spectrum sensing.
Spectrum sensing is the process of detecting the presence and characteristics of radio signals in a given frequency band. This is particularly important in cognitive radio systems, which aim to dynamically utilize unused spectrum. Imagine a radio station manager trying to figure out which frequencies are currently in use so they can broadcast without causing interference. Spectrum sensing is that manager’s tool.
Several methods for spectrum sensing exist:
- Energy Detection: This is a simple method that measures the total energy level of the received signal. If the energy exceeds a predefined threshold, a signal is assumed to be present. It’s simple but susceptible to noise uncertainty.
- Matched Filtering: This technique correlates the received signal with a known signal template. A high correlation indicates the presence of that specific signal. It’s more specific than energy detection but requires knowledge of the signal’s characteristics.
- Cyclostationary Feature Detection: This method exploits the periodic statistical properties of many modulated signals. It’s robust against noise but computationally more complex.
- Wavelet Transform-based Detection: This uses wavelet transforms to analyze the signal’s time-frequency characteristics, enabling better detection in non-stationary environments.
The choice of sensing method depends on factors such as the desired detection performance, computational complexity, and the nature of the radio environment. For instance, energy detection is suitable for initial spectrum exploration, while more sophisticated methods might be needed for reliable detection of weak signals or signals with unknown characteristics.
Q 13. What are the security considerations for advanced radio communication systems?
Security considerations for advanced radio communication systems are paramount, especially as these systems become increasingly critical for various applications. Protecting against unauthorized access, eavesdropping, and manipulation of transmitted data is crucial. Imagine a hospital’s wireless medical network – unauthorized access could have catastrophic consequences.
Key security considerations include:
- Authentication and Authorization: Ensuring only authorized devices and users can access the network and its resources. This could involve password protection, digital certificates, or more advanced cryptographic methods.
- Data Confidentiality: Protecting transmitted data from eavesdropping using encryption techniques, such as AES or other robust algorithms.
- Data Integrity: Ensuring the data has not been altered during transmission using message authentication codes (MACs) or digital signatures.
- Availability: Protecting the system from denial-of-service (DoS) attacks or other disruptions that prevent legitimate users from accessing the network.
- Secure Key Management: Establishing and managing cryptographic keys securely, as weak key management can negate other security measures.
- Physical Security: Protecting the physical infrastructure from unauthorized access or tampering.
Implementing robust security measures is essential for maintaining the confidentiality, integrity, and availability of advanced radio communication systems. This often involves a layered approach, combining various techniques to provide comprehensive protection.
Q 14. How do you design a robust communication system against jamming attacks?
Designing a robust communication system against jamming attacks requires a multifaceted approach, focusing on both prevention and mitigation. Jamming is like someone shouting loudly to drown out your conversation – it needs to be counteracted.
Strategies include:
- Frequency Hopping Spread Spectrum (FHSS): This technique rapidly changes the operating frequency, making it difficult for a jammer to continuously target the signal. Imagine a conversation that quickly switches topics – the jammer has trouble keeping up.
- Direct Sequence Spread Spectrum (DSSS): This spreads the signal across a wider bandwidth, making it harder to jam effectively. The signal is spread thinly, making it difficult to overwhelm.
- Adaptive Modulation and Coding: Adjusting the modulation scheme and error-correcting codes based on the channel conditions. If the channel is jammed, the system can adapt to maintain reliability.
- Redundancy: Using multiple communication paths or redundant components to tolerate jamming. If one path is jammed, another remains available.
- Beamforming: Using smart antennas to focus the signal in the direction of the receiver, reducing susceptibility to jamming from other directions.
- Jammer Detection and Mitigation: Implementing techniques to detect jamming attacks and respond accordingly, such as switching frequencies or employing interference cancellation techniques.
The optimal approach depends on the specific jamming scenario and the system’s constraints. Often, a combination of these techniques is employed for maximum protection. For example, a military communication system might use FHSS and beamforming to withstand sophisticated jamming attempts. Commercial applications might employ simpler methods like DSSS and adaptive modulation.
Q 15. Explain the concept of cognitive radio and its applications.
Cognitive radio is a revolutionary concept in wireless communication that allows a radio to intelligently sense its environment and adapt its transmission parameters to optimize performance and avoid interference. Imagine a radio that’s like a chameleon, changing its color (frequency) and its volume (power) to blend into its surroundings and communicate effectively. It dynamically adjusts its operating parameters based on the available spectrum, sharing it efficiently with other users.
Instead of rigidly adhering to pre-assigned frequencies, a cognitive radio can identify unused or underutilized spectrum and opportunistically utilize it. This improves spectrum efficiency, a crucial aspect given the ever-increasing demand for wireless communication.
- Applications: Cognitive radios have numerous applications, including:
- Dynamic Spectrum Access (DSA): Allowing secondary users to access spectrum licensed to primary users when it’s not being used.
- Improved Network Capacity: Increasing the overall capacity of wireless networks by efficiently using the available spectrum.
- Enhanced Wireless Sensor Networks: Enabling energy-efficient and flexible communication in sensor networks.
- Public Safety Communication: Providing reliable and robust communication during emergencies.
For example, in a crowded Wi-Fi environment, a cognitive radio-enabled device could find an available channel and switch to it, avoiding congestion and improving data rates. Another example is in military applications, where cognitive radios can adapt to jamming or interference, maintaining communication reliability even in hostile environments.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. What are the challenges in implementing software-defined radio?
Implementing software-defined radios (SDRs) presents several significant challenges:
- Complexity: Designing and implementing SDR software is extremely complex, requiring specialized expertise in digital signal processing (DSP), embedded systems, and radio frequency (RF) engineering. The software needs to be highly efficient to handle real-time signal processing, which is a non-trivial task.
- Real-time Processing Requirements: SDRs process signals in real-time, demanding high processing power and low latency. Meeting these requirements can be challenging, especially for high-bandwidth applications.
- Hardware limitations: While advances in hardware are continuous, the processing capabilities of embedded systems in SDRs may still limit the achievable performance, particularly in complex scenarios or with high data rates. The available processing power directly affects the complexity of the algorithms that can be implemented.
- Software Development and Debugging: Developing and debugging SDR software can be incredibly difficult due to the real-time constraints and the interaction of various hardware and software components. Thorough testing and validation are crucial.
- Cost: Development, testing and deployment of SDRs can be expensive, particularly for complex systems.
- Security vulnerabilities: The software nature of SDRs can make them vulnerable to cyberattacks, requiring careful security design and implementation. The open nature of SDR software increases this risk.
Consider a scenario where an SDR needs to perform complex modulation and demodulation schemes in real-time. The software needs to be optimized to ensure that the processing delay doesn’t lead to data loss or degradation of the communication quality. This is a considerable challenge that needs careful attention to algorithm design and hardware optimization.
Q 17. Describe the architecture of a typical software-defined radio system.
A typical SDR system architecture consists of several key components:
- RF Front-End: This is the interface between the SDR and the physical radio waves. It includes components like antennas, filters, mixers, and amplifiers, which handle the analog signal processing before it’s converted into digital form.
- Analog-to-Digital Converter (ADC): Converts the received analog signals into digital format, allowing the digital signal processor to process the data.
- Digital Signal Processor (DSP): The heart of the SDR, it performs all the digital signal processing tasks. These can include modulation, demodulation, channel equalization, error correction, and many more. This is typically a programmable processor which allows for flexibility in signal processing algorithms.
- Digital-to-Analog Converter (DAC): Converts the digitally processed signals back into analog form for transmission.
- RF Transmitter: Sends the analog signals over the air.
- Host Computer: Typically, a computer system interacts with the SDR, providing control, configuration, and data processing capabilities. This is where higher-level applications, such as modulation scheme selection or signal analysis tools, run.
The DSP often includes programmable functions like filtering, modulation/demodulation, and coding/decoding that are adaptable to changing communication needs. This flexibility is a key advantage of SDRs, as they are not limited to a fixed set of radio functionalities, unlike conventional radios. Think of it like a programmable music player – you can change the song (modulation), volume (power), and even add effects (channel coding).
Q 18. Explain different methods for power control in wireless networks.
Power control in wireless networks is crucial for optimizing energy efficiency, extending battery life, managing interference, and maximizing network capacity. Several methods are employed:
- Open-loop power control: This method uses pre-defined power levels based on the distance to the base station or other factors. It’s simple to implement but less efficient than closed-loop methods. Imagine shouting at different volumes depending on how far someone is.
- Closed-loop power control: This method dynamically adjusts the transmission power based on feedback from the receiver, ensuring a constant received signal strength. Think of a speaker system automatically adjusting its volume to match the background noise.
- Distributed power control: In this approach, each node independently adjusts its power level based on local information and possibly using algorithms like game theory or iterative methods to find an optimal power setting for the entire network. It’s decentralized and suitable for large networks.
- Proportional fair power control: This method allocates power to users proportionally based on their signal quality, ensuring fairness among the users. It balances performance and fairness.
For example, in a cellular network, closed-loop power control ensures that each user’s signal is strong enough to be received without excessive power, saving energy and reducing interference. In a sensor network, distributed power control can be used to manage power usage efficiently while ensuring network connectivity.
Q 19. What are the considerations for designing a low-power wireless communication system?
Designing low-power wireless communication systems involves several crucial considerations:
- Hardware Selection: Choose energy-efficient components, such as low-power microcontrollers, RF transceivers, and power management integrated circuits (PMICs).
- Protocol Optimization: Utilize energy-efficient communication protocols such as Bluetooth Low Energy (BLE) or Zigbee. These protocols are designed for low power consumption.
- Power Management Techniques: Implement power management techniques like duty cycling (periodically turning off the radio), sleep modes, and adaptive power control. Duty cycling is like turning off the lights when you leave a room to save energy.
- Efficient Modulation and Coding: Select modulation and coding schemes that offer a good trade-off between data rate and power consumption. Some schemes are inherently more energy efficient than others.
- Antenna Design: Use high-efficiency antennas to maximize the radiated power and minimize power loss.
- Software Optimization: Minimize the processing load on the microcontroller to reduce power consumption. Optimization can be done by using efficient algorithms and reducing unnecessary computations.
For instance, in a wireless sensor network deployed in a remote area, minimizing power consumption is crucial as battery replacement can be difficult or impossible. By carefully selecting low-power components, using energy-efficient protocols, and implementing power management techniques, the lifetime of the sensors can be significantly extended.
Q 20. How do you measure the bit error rate (BER) of a wireless communication system?
The bit error rate (BER) measures the frequency of errors in data transmission. To measure the BER of a wireless communication system, you typically:
- Transmit a known data sequence: Send a predefined sequence of bits over the wireless channel. The sequence should be long enough to achieve statistically significant results.
- Receive and compare: Receive the transmitted sequence at the receiver end. Compare the received bits with the original transmitted bits to identify errors.
- Count the errors: Count the number of bits that were received incorrectly.
- Calculate the BER: The BER is calculated as the ratio of the number of erroneous bits to the total number of transmitted bits.
BER = (Number of erroneous bits) / (Total number of transmitted bits) - Repeat and average: Repeat the process multiple times under the same conditions and average the BER values to obtain a more accurate result. This accounts for random noise and variations in the channel.
Specialized test equipment, such as vector signal analyzers or bit error rate testers (BERTs), can automate this process and provide accurate BER measurements. Simulations can also be used, especially when dealing with controlled channel conditions.
Q 21. Explain different methods for synchronization in wireless communication systems.
Synchronization in wireless communication is crucial for successful data transmission and reception. Different methods are used:
- Time Synchronization: Ensures that the transmitter and receiver clocks are synchronized to the same time base. This is essential for accurate timing of data transmission and reception. Techniques like GPS or Network Time Protocol (NTP) are often employed.
- Frequency Synchronization: Ensures that the transmitter and receiver oscillators are synchronized to the same frequency. This is crucial for preventing signal distortion and maintaining coherence. Methods like phase-locked loops (PLLs) are often used.
- Frame Synchronization: This involves the receiver identifying the beginning and end of each data frame. This often involves unique frame synchronization sequences or headers that the receiver searches for in the incoming data stream.
- Carrier Synchronization: Involves synchronizing to the carrier signal of the transmitted signal. This ensures that the demodulator can accurately extract the data from the received signal. This is often done using correlation or other signal processing techniques.
- Symbol Synchronization: Involves aligning the received symbols in the digital signal processing to their correct timing slots. This is necessary to ensure that the samples are correctly aligned with the transmitted symbols.
For example, in GPS, time synchronization is essential for determining the precise location of a receiver. In cellular networks, carrier and symbol synchronization are crucial for ensuring that the base station can correctly decode the information transmitted by mobile devices.
Q 22. What are the principles of network coding?
Network coding fundamentally changes how data is transmitted in a network. Instead of simply forwarding packets, network coding allows intermediate nodes to combine multiple packets received from different sources, creating new packets that contain encoded information from the original sources. This encoded information is then forwarded to the destination. The destination node, using appropriate decoding techniques, can then reconstruct the original data packets. The key benefit is increased throughput and robustness against packet loss, particularly in wireless networks where signal quality can fluctuate.
Imagine a scenario with two sources, A and B, each sending a packet (Packet A and Packet B) to a destination. In traditional routing, the destination receives these packets independently. With network coding, an intermediate node can add Packet A and Packet B together (e.g., bitwise XOR). The destination then receives this encoded packet which contains information from both A and B. Knowing the encoding scheme, the destination can recover both original packets, assuming no errors occurred during the transmission of the combined packet. The strategy is resilient to packet loss because if one of the original packets gets lost, the destination can still partially recover the lost data from the encoded combination.
- Increased throughput: Efficient use of bandwidth by combining data streams.
- Enhanced reliability: Resilience to packet loss and interference.
- Reduced latency: Faster delivery of data in certain scenarios.
Q 23. How do you optimize the performance of a wireless communication system in a fading channel?
Optimizing wireless communication in fading channels requires a multi-faceted approach. Fading, the variation of signal strength over time and space, severely impacts reliability and data rate. Here’s a breakdown of key techniques:
- Diversity Techniques: These exploit the fact that fading is often independent across different paths or antennas. Examples include spatial diversity (multiple antennas), frequency diversity (spreading the signal over multiple frequencies), and time diversity (repeating transmissions). Spatial diversity with multiple-input and multiple-output (MIMO) systems is particularly effective.
- Adaptive Modulation and Coding (AMC): This adjusts the modulation scheme (e.g., BPSK, QAM) and coding rate based on the instantaneous channel conditions. When the channel is strong, higher-order modulation schemes can be used to increase the data rate. Conversely, during deep fades, lower-order modulation schemes with more robust error correction codes are used to ensure reliability. AMC requires accurate and timely channel state information (CSI).
- Channel Equalization: This aims to compensate for the distortion introduced by the channel. Techniques like linear equalization and decision-feedback equalization are used to mitigate intersymbol interference (ISI), which causes adjacent symbols to overlap and interfere with each other. This is particularly crucial in high-data-rate systems operating in multipath environments.
- Power Control: Adjusting the transmit power dynamically based on the channel condition can improve reliability and reduce interference to other users. Techniques like closed-loop power control rely on feedback from the receiver, while open-loop techniques use estimated channel information.
For example, in a cellular network, a base station might use AMC to switch between different modulation schemes depending on the signal strength received from each mobile device. A weaker signal might use BPSK with strong forward error correction, while a stronger signal might employ higher-order modulation like 64-QAM.
Q 24. Describe the different layers of the OSI model and their relevance to radio communication.
The Open Systems Interconnection (OSI) model is a conceptual framework that divides network communication into seven distinct layers. Each layer performs specific functions, and they interact with adjacent layers to provide a complete communication service. In the context of radio communication, each layer plays a crucial role:
- Layer 7 (Application): This layer defines the network applications and services, such as web browsing, email, file transfer. In radio communication, this could include protocols for satellite navigation (GPS) or wireless sensor networks.
- Layer 6 (Presentation): This layer handles data formatting, encryption, and compression. For example, encrypting voice data before transmission in a secure radio communication system.
- Layer 5 (Session): This layer manages sessions between communicating devices, such as establishing, maintaining, and terminating connections. This could involve handshaking processes in wireless networks.
- Layer 4 (Transport): This layer ensures reliable data delivery between applications, providing error control and flow control. Protocols like TCP and UDP are examples at this layer. These protocols are crucial for reliable data transfer in radio networks.
- Layer 3 (Network): This layer handles routing and logical addressing. IP addressing and routing protocols are vital here, determining the path a radio signal takes through a network.
- Layer 2 (Data Link): This layer deals with physical addressing and error detection/correction on a point-to-point link. Ethernet and WiFi protocols operate at this layer. In radio, this is where media access control (MAC) protocols, such as CSMA, operate.
- Layer 1 (Physical): This layer handles the physical transmission of data, including modulation, demodulation, and signal characteristics. This layer is directly involved in radio wave propagation, antenna design, and signal processing at the transceiver level.
Understanding the OSI model provides a structured approach to troubleshooting and designing complex radio communication systems.
Q 25. Explain the concept of carrier sense multiple access (CSMA).
Carrier Sense Multiple Access (CSMA) is a media access control (MAC) protocol used in shared-medium networks, including wireless networks, to coordinate access to the transmission medium. It’s based on the principle that a device should listen before transmitting. The idea is to avoid collisions between transmissions by different devices.
The basic process is as follows: Before transmitting, a device ‘senses’ the carrier (checks if the channel is busy). If the channel is idle, the device begins transmission. If the channel is busy, the device waits for a period of time and then senses the channel again. There are variations of CSMA:
- CSMA/CD (Collision Detection): Devices detect collisions during transmission and stop transmitting, using a backoff algorithm to reschedule the transmission. This is primarily used in wired Ethernet networks.
- CSMA/CA (Collision Avoidance): Devices attempt to avoid collisions using techniques like random backoff and acknowledgment mechanisms. This is commonly used in wireless networks like Wi-Fi (802.11). The use of ACKs provides a confirmation to the transmitter that the packet has been successfully received.
Imagine a group of people trying to speak at the same time. In CSMA/CA, each person listens before speaking. If they hear someone else, they wait a random amount of time and then try again. The randomness helps prevent repeated collisions.
Q 26. What is the difference between narrowband and wideband communication?
The key difference between narrowband and wideband communication lies in the bandwidth they utilize:
- Narrowband Communication: Uses a small portion of the radio frequency spectrum. It’s characterized by low data rates and is more susceptible to noise and interference. Narrowband systems are often more efficient in terms of power usage because they concentrate their power within a narrow frequency range. Examples include AM radio and some older cellular systems.
- Wideband Communication: Uses a large portion of the radio frequency spectrum. This allows for significantly higher data rates compared to narrowband. Wideband systems are often more robust to multipath fading and interference due to the inherent diversity. Examples include Wi-Fi, 4G/5G cellular networks, and ultra-wideband (UWB) systems.
An analogy is comparing a single lane road (narrowband) to a highway with multiple lanes (wideband). The highway allows for much faster travel (higher data rates) with more capacity, though it requires more resources.
Q 27. Describe your experience with different radio frequency test equipment.
Throughout my career, I’ve extensively used various radio frequency (RF) test equipment. My experience encompasses both laboratory and field testing scenarios. This includes:
- Signal Generators: For generating test signals with specific frequencies, amplitudes, and modulation schemes. I’ve utilized instruments from Keysight and Rohde & Schwarz to test the sensitivity and selectivity of receivers.
- Spectrum Analyzers: These are essential for analyzing the frequency content of signals, identifying interference, and measuring signal power and characteristics. I am proficient with spectrum analyzers from Agilent and Tektronix, frequently using them for channel characterization and troubleshooting.
- Network Analyzers: Used to characterize the performance of antennas and transmission lines. I’ve used these tools to measure scattering parameters (S-parameters) and optimize antenna design and impedance matching.
- Vector Signal Analyzers (VSAs): For advanced signal analysis, including measuring complex modulation formats and evaluating signal quality. VSAs have been instrumental in my work evaluating the performance of modern communication systems like OFDM.
- Power Meters: For measuring the power levels of RF signals, crucial for ensuring compliance with regulatory standards and for optimizing transmitter performance.
- EMI/EMC Test Equipment: For compliance testing of RF equipment to ensure that they meet emission and immunity standards.
My experience extends to using these instruments for tasks such as characterizing fading channels, measuring antenna gain and efficiency, evaluating the performance of modulation techniques, and troubleshooting RF systems. I am adept at interpreting measurement results and translating them into actionable insights for system optimization.
Key Topics to Learn for Advanced Radio Communication Interview
- Modulation Techniques: Understand various modulation schemes (e.g., FSK, PSK, QAM) and their applications in different communication scenarios. Consider the trade-offs between bandwidth efficiency, power efficiency, and robustness to noise.
- Signal Processing: Master concepts like filtering, equalization, and synchronization. Be prepared to discuss practical applications such as channel equalization in fading environments or clock recovery in digital communication systems.
- Antenna Theory and Design: Explore different antenna types and their radiation patterns. Understand concepts like impedance matching, gain, and polarization, and be ready to discuss practical antenna selection for specific applications.
- Propagation Models: Familiarize yourself with different propagation models (e.g., free space path loss, ray tracing) and their application in predicting signal strength and coverage. Understand the impact of factors like multipath propagation and fading.
- Network Protocols: Gain a thorough understanding of relevant network protocols used in advanced radio communication systems. This includes protocols for control, data transfer, and error correction.
- Error Correction Codes: Learn about different error correction techniques and their implementation in radio communication systems. Discuss the trade-offs between coding complexity and error correction capability.
- System Design and Optimization: Be ready to discuss the overall system design process, including considerations for power, bandwidth, and reliability. Understand methods for optimizing system performance.
- Troubleshooting and Problem-Solving: Practice identifying and resolving common issues in advanced radio communication systems. Be prepared to discuss systematic troubleshooting approaches.
Next Steps
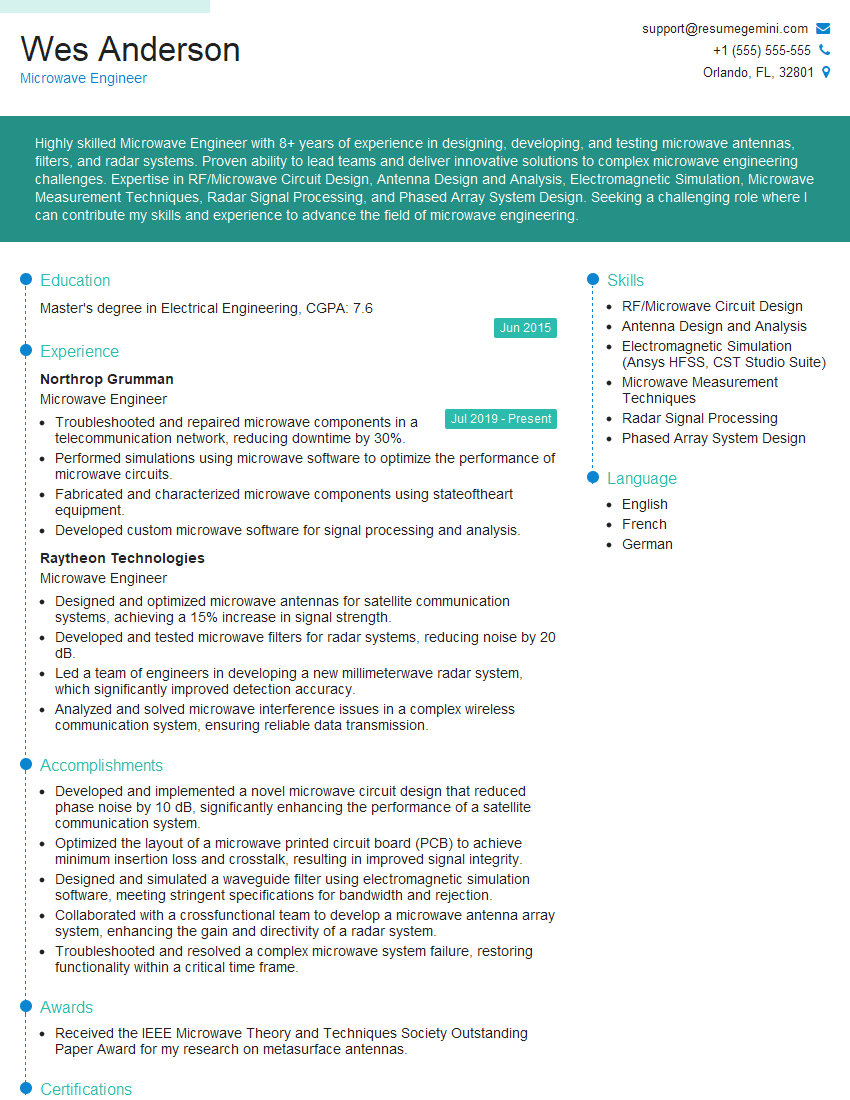
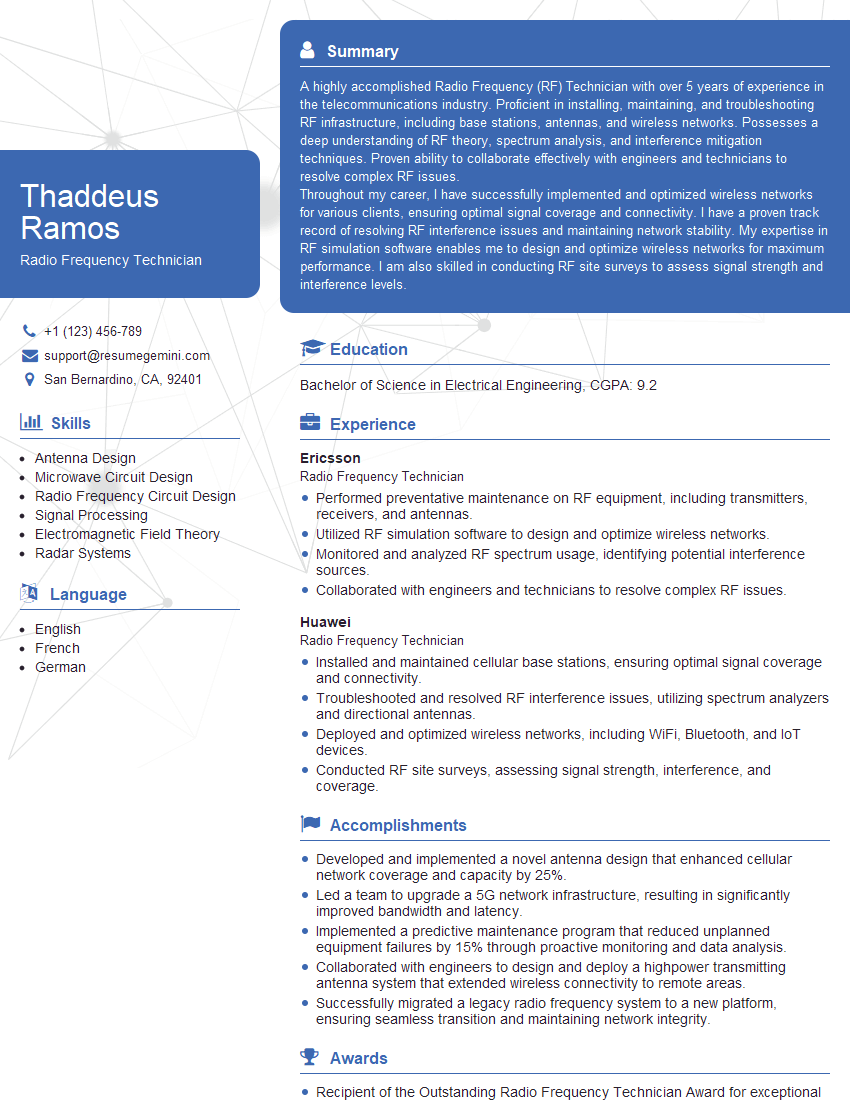
Mastering Advanced Radio Communication opens doors to exciting and rewarding careers in various fields, including telecommunications, aerospace, and defense. To maximize your job prospects, it’s crucial to present your skills and experience effectively. Creating an ATS-friendly resume is key to getting your application noticed. We highly recommend using ResumeGemini to build a professional and impactful resume that highlights your expertise. ResumeGemini provides tools and resources, including examples of resumes tailored to Advanced Radio Communication, to help you craft a compelling document that showcases your qualifications for your dream role.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Really detailed insights and content, thank you for writing this detailed article.
IT gave me an insight and words to use and be able to think of examples