Feeling uncertain about what to expect in your upcoming interview? We’ve got you covered! This blog highlights the most important Experience with Compliance and Auditing interview questions and provides actionable advice to help you stand out as the ideal candidate. Let’s pave the way for your success.
Questions Asked in Experience with Compliance and Auditing Interview
Q 1. Explain the difference between compliance and auditing.
Compliance and auditing are closely related but distinct concepts. Compliance focuses on ensuring adherence to rules, regulations, laws, and internal policies. It’s about doing the right thing according to established standards. Auditing, on the other hand, is the systematic and independent examination of an organization’s activities to determine whether those activities comply with established criteria. It’s about verifying that the right things are being done. Think of it this way: compliance is the destination, and auditing is the process of checking if you’ve arrived there.
For example, a company might have a compliance program to ensure data privacy (compliance). An auditor would then review the company’s processes and documentation to determine if the company is actually following its own data privacy policies and regulations (auditing).
Q 2. Describe your experience with SOX compliance.
I have extensive experience with SOX (Sarbanes-Oxley Act) compliance, having led multiple SOX compliance initiatives in previous roles. My experience includes developing and implementing SOX control frameworks, conducting risk assessments, documenting processes, and testing the effectiveness of internal controls over financial reporting. This encompassed working with cross-functional teams, including finance, IT, and operations, to ensure all aspects of SOX compliance were met. I’m proficient in using various tools and techniques to streamline the SOX compliance process and improve efficiency. For example, in one role, I implemented a centralized documentation system using a project management software to improve transparency and collaboration, leading to a significant reduction in SOX audit findings.
Q 3. How do you identify and assess compliance risks?
Identifying and assessing compliance risks requires a systematic approach. I typically begin with a thorough understanding of the applicable laws, regulations, and industry standards. Then, I perform a risk assessment, using a combination of methods such as:
- Top-down risk assessment: Starting with high-level risks and then drilling down to specific areas.
- Bottom-up risk assessment: Identifying risks at the process level and aggregating them to higher levels.
- Workshops and interviews: Engaging with key stakeholders to understand their perspectives and identify potential risks.
- Data analysis: Reviewing key performance indicators (KPIs) and other data to identify trends and anomalies that might indicate potential compliance issues.
Once risks are identified, I prioritize them based on their likelihood and potential impact, developing mitigation strategies to address the highest-priority risks first. This usually involves a combination of preventative and detective controls.
Q 4. What is your experience with internal control frameworks (e.g., COSO)?
I’m highly familiar with internal control frameworks, particularly COSO (Committee of Sponsoring Organizations of the Treadway Commission). My experience includes designing, implementing, and testing internal controls based on the COSO framework. I understand the five components of the COSO framework: control environment, risk assessment, control activities, information and communication, and monitoring activities. I have used this framework to develop and implement effective internal controls across various functions, resulting in improved operational efficiency and risk mitigation. For example, in a previous role, I helped a company implement a new inventory management system based on COSO principles, leading to significant reductions in inventory shrinkage and improved financial reporting accuracy.
Q 5. Explain your approach to conducting an internal audit.
My approach to conducting an internal audit is methodical and risk-based. It begins with a thorough understanding of the audit objectives and scope. I then develop a detailed audit plan that includes:
- Risk assessment: Identifying areas of high risk based on previous audits, regulatory changes, or other factors.
- Testing procedures: Selecting appropriate audit procedures such as walkthroughs, document review, and testing of controls.
- Sampling methodology: Selecting samples that are representative of the population being audited.
- Documentation: Maintaining detailed audit documentation, including audit programs, working papers, and findings.
Throughout the audit, I maintain open communication with the auditee to ensure transparency and address any questions or concerns. The audit culminates in a comprehensive report summarizing the findings, conclusions, and recommendations.
Q 6. How do you ensure the objectivity and independence of an audit?
Ensuring objectivity and independence in an audit is paramount. This is achieved through several key measures:
- Organizational Structure: The audit function should report to a senior management level independent of the operations being audited. This creates a distance that promotes unbiased assessment.
- Competence and Training: Auditors must possess the necessary skills, knowledge, and experience, along with ongoing professional development to remain current with best practices and regulations.
- Due Professional Care: Auditors must conduct themselves with integrity and professional skepticism, objectively gathering and evaluating evidence.
- Documentation and Review: All work must be properly documented and reviewed by peers or supervisors to ensure the quality and consistency of the audit process.
- Rotation of Auditors: Regular rotation of audit team members helps prevent bias and ensures fresh perspectives on processes and controls.
These measures collectively build a framework that safeguards against potential biases and guarantees the integrity of the audit findings.
Q 7. Describe a situation where you identified a compliance gap. How did you address it?
During an audit of a client’s IT security controls, I identified a significant compliance gap concerning data encryption. While the company had a policy mandating data encryption, it wasn’t consistently implemented across all systems and databases. This posed a substantial risk of data breaches and non-compliance with relevant regulations like GDPR.
To address this, I first documented the gap thoroughly, detailing the affected systems and the extent of the non-compliance. I then collaborated with the IT department to develop a remediation plan, which involved:
- Prioritizing systems based on risk and sensitivity of data.
- Implementing encryption solutions for high-risk systems.
- Developing a training program for IT staff on proper encryption procedures.
- Creating a monitoring system to ensure ongoing compliance.
The remediation plan was successfully implemented, and subsequent audits confirmed the closure of the compliance gap. The key to success was open communication, clear documentation, and a collaborative approach to problem-solving.
Q 8. What are the key components of a comprehensive compliance program?
A comprehensive compliance program isn’t a one-size-fits-all solution; it’s tailored to an organization’s specific risks and regulatory landscape. However, several key components consistently appear. Think of it like building a house – you need a solid foundation and various interconnected systems.
- Risk Assessment: This is the foundation. It involves identifying potential compliance risks, analyzing their likelihood and impact, and prioritizing them. For example, a hospital would heavily prioritize HIPAA compliance risks, while a financial institution would focus on regulations like SOX (Sarbanes-Oxley Act).
- Policies and Procedures: These are the blueprints. Clearly written policies and procedures outline how the organization will comply with regulations. They should be readily accessible to all employees and regularly reviewed and updated.
- Training and Awareness: This is the workforce. Regular training ensures employees understand their roles and responsibilities in maintaining compliance. Interactive modules, scenario-based exercises, and regular reminders keep compliance top-of-mind.
- Monitoring and Auditing: This is the ongoing inspection. Regular monitoring and internal audits help identify weaknesses and ensure the program’s effectiveness. This could include data sampling, system checks, and employee interviews.
- Reporting and Remediation: This is the feedback loop. Regular reporting on compliance status helps identify areas for improvement. A clear process for remediation of identified issues is crucial.
- Management Oversight and Accountability: This is the leadership. Senior management must demonstrate commitment to compliance by actively overseeing the program and holding individuals accountable for their roles.
In essence, a robust compliance program is proactive, not reactive, continually adapting to changing regulations and the organization’s evolving needs.
Q 9. How familiar are you with relevant regulations (e.g., HIPAA, GDPR)?
I possess extensive familiarity with a range of relevant regulations. My experience includes working directly with HIPAA (Health Insurance Portability and Accountability Act), GDPR (General Data Protection Regulation), and other industry-specific regulations depending on the client.
For example, when working with a healthcare provider, ensuring HIPAA compliance involved reviewing their processes for handling Protected Health Information (PHI), conducting audits of their electronic health records system, and ensuring employee training on HIPAA regulations. With a European client, understanding GDPR involved focusing on data subject rights, cross-border data transfers, and data security measures. I understand the nuances of each regulation, including the penalties for non-compliance and the specific requirements for data privacy and security.
Q 10. How do you prioritize audit findings?
Prioritizing audit findings requires a structured approach. I utilize a risk-based prioritization framework, considering factors like:
- Risk Severity: This assesses the potential impact of the non-compliance. A critical finding with high potential for financial loss or reputational damage takes precedence.
- Likelihood of Occurrence: How likely is the identified weakness to lead to a breach or violation? High-likelihood issues require immediate attention.
- Regulatory Impact: Are the findings related to high-profile regulations with significant penalties (e.g., a GDPR violation)? Regulatory impact significantly increases priority.
- Urgency: Some findings, while not necessarily the most severe, might require immediate action to mitigate imminent risks.
I typically use a matrix or scoring system to rank findings based on these criteria. For instance, a high severity, high likelihood, and high regulatory impact finding would be a top priority, while a low severity, low likelihood, and low regulatory impact finding would have a lower priority.
Q 11. Explain your experience with audit reporting and communication.
My audit reporting experience includes creating clear, concise, and comprehensive reports that highlight key findings, root causes, and recommended actions. I tailor reports to the audience, using executive summaries for senior management and more detailed explanations for operational teams.
I have experience with various reporting tools and methods, including using data visualization techniques to effectively communicate findings. For instance, I might use charts and graphs to show trends in non-compliance or the distribution of risks across different departments. I always ensure that my reports are factual, objective, and well-supported by evidence.
Communication is key. I conduct follow-up meetings to discuss findings and answer questions. I also facilitate the remediation process by working with management to implement corrective actions and monitor their effectiveness.
Q 12. How do you handle disagreements with management regarding audit findings?
Disagreements with management regarding audit findings are a possibility, and handling them professionally is essential. My approach involves:
- Objective Evidence: I ensure that all findings are supported by concrete evidence, such as documentation, logs, or interview transcripts. This forms the basis of a reasoned discussion.
- Professional Communication: I communicate my findings calmly and clearly, focusing on the facts and potential risks, not on assigning blame.
- Collaborative Approach: I work with management to find common ground and collaboratively develop solutions. This might involve adjusting my recommendations based on their input or exploring alternative mitigation strategies.
- Escalation Process: If disagreements persist, I follow the organization’s established escalation procedures, documenting all communications and decisions made.
- Documentation: Throughout the process, I maintain meticulous documentation of all discussions, agreements, and decisions to protect myself and the organization.
The goal is to reach a mutually agreeable solution that effectively mitigates the identified risks while maintaining a positive working relationship.
Q 13. Describe your experience with data analytics in auditing.
Data analytics plays a vital role in modern auditing. I’m proficient in using data analytics techniques to identify trends, patterns, and anomalies in large datasets. This allows for more efficient and effective audits.
For example, I’ve used data analytics to identify unusual activity in financial transactions, flag potential security breaches, and assess the effectiveness of compliance controls. Specific tools and techniques I’ve used include SQL queries for database analysis, scripting languages like Python for data manipulation and analysis, and data visualization tools to create compelling reports. The application of data analytics significantly enhances the depth and accuracy of audit findings, allowing for a more risk-focused and proactive approach.
Q 14. What is your understanding of risk assessment methodologies?
My understanding of risk assessment methodologies encompasses several well-established frameworks. These frameworks provide a structured approach to identifying, analyzing, and mitigating potential risks. Some common methodologies I’m familiar with include:
- NIST Cybersecurity Framework: A widely adopted framework for managing cybersecurity risks.
- COSO Framework: A comprehensive framework for enterprise risk management, often used in financial institutions.
- ISO 31000: An international standard that provides principles and guidelines for risk management.
These frameworks often involve a combination of qualitative and quantitative analysis, incorporating factors such as the likelihood and impact of risks. A thorough risk assessment allows for the prioritization of resources and the development of targeted controls to mitigate the most critical risks.
Regardless of the specific framework, the key elements remain consistent: identifying potential risks, assessing their likelihood and impact, evaluating existing controls, and developing a plan to mitigate residual risks. It’s about a proactive and informed approach to managing uncertainty.
Q 15. How do you ensure the accuracy and completeness of audit evidence?
Ensuring the accuracy and completeness of audit evidence is paramount to a successful audit. It’s like building a house – you need a strong foundation of reliable information. This involves a multi-faceted approach.
Proper Documentation: Meticulous record-keeping is crucial. Every piece of evidence should be clearly labeled, dated, and sourced. This includes documenting the source of the information, the method of obtaining it, and any limitations.
Verification and Cross-Referencing: Don’t rely on a single source. Cross-reference information from multiple sources to corroborate findings. For example, if reviewing financial records, I would compare data from the general ledger to supporting documentation like invoices and bank statements.
Sampling Techniques: Employ appropriate statistical sampling methods (discussed further in another question) to select a representative sample of evidence while ensuring the sample size is adequate to support conclusions. Improper sampling can lead to inaccurate results.
Data Analytics: Leveraging data analytics tools can significantly improve accuracy and efficiency in analyzing large datasets. This can reveal anomalies or inconsistencies that might be missed through manual review.
Professional Skepticism: Maintain a questioning mind throughout the audit process. Don’t just accept information at face value; critically evaluate the evidence and look for potential biases or inconsistencies.
For example, in an IT audit, verifying access controls, I wouldn’t just rely on the system’s access logs. I’d also interview users to understand their access needs and cross-reference with the organization’s access control policy.
Career Expert Tips:
- Ace those interviews! Prepare effectively by reviewing the Top 50 Most Common Interview Questions on ResumeGemini.
- Navigate your job search with confidence! Explore a wide range of Career Tips on ResumeGemini. Learn about common challenges and recommendations to overcome them.
- Craft the perfect resume! Master the Art of Resume Writing with ResumeGemini’s guide. Showcase your unique qualifications and achievements effectively.
- Don’t miss out on holiday savings! Build your dream resume with ResumeGemini’s ATS optimized templates.
Q 16. How do you stay updated on changes in compliance regulations?
Staying current with compliance regulations is an ongoing process, much like keeping a garden flourishing. It requires consistent effort and attention to detail.
Subscription to Regulatory Updates: I subscribe to relevant newsletters, journals, and online resources published by regulatory bodies such as the SEC, FCA (if relevant to the region), or industry-specific organizations. This provides timely alerts on changes.
Professional Development: Attending webinars, conferences, and workshops keeps me informed about the latest interpretations and best practices in compliance. It also allows for networking with other professionals in the field.
Monitoring Regulatory Websites: I regularly check the websites of relevant regulatory bodies for announcements, updates, and guidance.
Networking with Peers: Engaging with colleagues and professional organizations allows for the exchange of information and insights on emerging compliance issues.
For instance, with the ever-evolving landscape of data privacy regulations like GDPR and CCPA, continuous learning is essential to stay compliant and advise clients effectively.
Q 17. What is your experience with audit sampling techniques?
Audit sampling is a crucial technique for efficiently evaluating a large population of data. It’s like tasting a spoonful of soup to determine the flavor of the whole pot. However, choosing the right technique is key.
Statistical Sampling: This method uses statistical principles to select a sample that is representative of the entire population. Techniques include random sampling, stratified sampling (dividing the population into strata and sampling from each), and systematic sampling (selecting every nth item).
Non-statistical Sampling: This involves judgmental selection of items based on auditor’s professional judgment and experience. While efficient, it poses higher risk of bias.
Example: In a financial statement audit, I might use stratified sampling to select a sample of invoices based on their dollar value (stratifying by high, medium, and low value) to ensure a proper representation of the overall population.
The choice of sampling technique depends on factors like the materiality of the items being audited, the risk of error, and the resources available. Properly documenting the sampling methodology and rationale is crucial to ensure auditability and defensibility.
Q 18. Describe your experience with different audit methodologies.
My experience encompasses various audit methodologies, each tailored to specific objectives and circumstances. Think of it like having different tools in a toolbox for different jobs.
Compliance Audits: These focus on verifying adherence to specific regulations, laws, or internal policies. I’ve conducted compliance audits for SOX (Sarbanes-Oxley Act), HIPAA (Health Insurance Portability and Accountability Act), and GDPR (General Data Protection Regulation).
Financial Audits: These audits examine the financial statements of an organization to assess their accuracy and reliability. This involves verifying transactions, balances, and disclosures.
Operational Audits: These evaluations assess the efficiency and effectiveness of an organization’s operations. They often look at internal controls, processes, and resource utilization.
IT Audits: These audits evaluate the security, integrity, and reliability of an organization’s information systems. This covers areas like cybersecurity, data governance, and system controls.
My approach involves understanding the specific audit objectives, identifying key risks, developing a comprehensive audit plan, and documenting the findings thoroughly. I am proficient in using various audit software and tools to streamline the process.
Q 19. How do you manage audit deadlines and resources effectively?
Managing audit deadlines and resources effectively is akin to orchestrating a complex project. It requires careful planning, prioritization, and strong communication.
Project Planning: Developing a detailed audit plan with clearly defined timelines and milestones is the foundation. This involves breaking down the audit into manageable tasks, assigning responsibilities, and establishing clear deadlines.
Resource Allocation: Efficient allocation of resources (personnel, technology, budget) is critical. This requires accurate estimations of the time and effort required for each task and ensuring sufficient resources are available.
Risk Management: Identifying and mitigating potential risks (delays, resource constraints, unexpected issues) is crucial. This includes establishing contingency plans.
Communication: Open and clear communication with the audit team, management, and stakeholders is essential. Regular updates and progress reports help maintain transparency and manage expectations.
Tools and Technologies: Utilizing project management software and audit automation tools can significantly improve efficiency and facilitate better resource allocation.
For instance, in a large-scale audit, I would utilize project management tools to track progress, manage tasks, and ensure adherence to deadlines, providing regular updates to stakeholders.
Q 20. What are your strengths and weaknesses as an auditor?
As an auditor, my greatest strengths are my attention to detail, analytical skills, and ability to communicate complex information clearly and concisely.
Attention to Detail: I am meticulous in my work, ensuring that all aspects of the audit are thoroughly examined. This helps identify even subtle errors or inconsistencies.
Analytical Skills: I am adept at identifying patterns, trends, and anomalies in data, allowing me to draw accurate conclusions and make informed recommendations.
Communication Skills: I can effectively communicate complex technical information to both technical and non-technical audiences. This ensures transparency and understanding throughout the audit process.
My primary area for development is delegation. While I am proficient in handling multiple tasks independently, I am working on improving my ability to effectively delegate responsibilities within a team to improve efficiency and overall workflow.
Q 21. Describe your experience with documenting audit procedures.
Thorough documentation of audit procedures is the cornerstone of a successful and defensible audit. It’s the audit’s historical record, much like a scientist’s detailed lab notebook.
Audit Plan: This outlines the scope, objectives, methodology, and timelines of the audit. It acts as a roadmap for the entire process.
Working Papers: These documents detail the evidence gathered, the procedures performed, the findings, and the conclusions reached. They provide a detailed audit trail.
Audit Reports: These formal reports summarize the audit findings, conclusions, and recommendations. They communicate the results to management and stakeholders.
Technology: Audit management software can streamline documentation by providing a central repository for all audit-related documents and facilitating workflow.
For example, when conducting an IT security audit, I would document the specific steps taken to test firewall configurations, access controls, and vulnerability scans, including the dates, times, and results of each test. This meticulous documentation ensures that the audit process is transparent, repeatable, and defensible.
Q 22. How do you handle confidential information during an audit?
Handling confidential information during an audit is paramount. It requires strict adherence to both legal and ethical guidelines. My approach involves a multi-layered strategy focusing on access control, secure storage, and data destruction.
Access Control: I utilize a need-to-know basis, ensuring only authorized personnel with a legitimate business need have access to sensitive data. This might involve password-protected documents, secure network access, and role-based permissions within audit management systems. For example, during a financial audit, only the audit team and relevant client personnel will have access to financial statements and supporting documentation.
Secure Storage: Physical documents are kept in locked cabinets or secure rooms. Digital information is stored on encrypted drives and accessed via secure networks with robust firewalls and intrusion detection systems. Consider, for instance, encrypting client data residing on laptops or USB drives used during fieldwork.
Data Destruction: After the audit is concluded and the required retention periods have elapsed, all confidential information is securely destroyed, either through shredding of physical documents or secure deletion of digital data. This ensures data privacy and compliance with regulations.
Ultimately, my commitment to confidentiality reflects my professional responsibility and commitment to maintaining the integrity of the audit process.
Q 23. What is your experience with using audit software?
I have extensive experience utilizing various audit software packages, including ACL, IDEA, and AuditCommand. These tools significantly enhance the efficiency and effectiveness of the audit process. My experience spans data extraction, analysis, testing, and reporting.
Data Extraction: I’m adept at using these tools to extract large datasets from various sources, including databases and spreadsheets. For example, using SQL queries within ACL to extract specific transaction data from a company’s database.
Data Analysis: I leverage analytical features such as data sampling, statistical analysis, and data visualization to identify anomalies and potential risks. This might involve using IDEA to perform Benford’s Law analysis to detect potential fraud.
Testing: I use audit software to perform various audit tests, such as substantive testing, compliance testing, and analytical procedures. For instance, using AuditCommand to automate the testing of internal controls.
Reporting: The software facilitates creating comprehensive audit reports, including data visualizations and key findings. This often streamlines the reporting process and ensures consistent, high-quality deliverables.
My proficiency with audit software allows me to conduct audits more efficiently, enabling a more thorough and in-depth analysis.
Q 24. How do you maintain professional skepticism during an audit?
Maintaining professional skepticism is crucial for a successful audit. It means questioning information, assumptions, and evidence, rather than accepting them at face value. I actively cultivate this mindset through several approaches:
Questioning Attitude: I consistently challenge management’s assertions and actively seek corroborating evidence from multiple independent sources. For example, if management states inventory levels are accurate, I would verify this through physical observation and independent inventory counts.
Critical Assessment: I critically evaluate all evidence obtained, considering its source, reliability, and potential biases. I would consider the internal control environment when assessing the reliability of financial records.
Professional Judgment: I rely on my professional judgment and experience to assess the validity of evidence and make informed decisions. This involves recognizing inconsistencies and ambiguities and determining their significance.
Documentation: I meticulously document all audit procedures, findings, and conclusions, ensuring a clear audit trail and demonstrating my skeptical approach. This supports the audit’s transparency and defensibility.
Maintaining professional skepticism is an ongoing process, requiring continuous vigilance and a commitment to objectivity.
Q 25. Explain your understanding of fraud risk management.
Fraud risk management is a systematic process designed to prevent, detect, and respond to fraudulent activities. It involves understanding the risks, implementing controls, and monitoring for potential fraud. A comprehensive program typically includes:
Risk Assessment: Identifying and assessing the potential for fraud within an organization. This includes evaluating the inherent risks (e.g., industry trends) and control risks (e.g., weaknesses in internal controls).
Control Design & Implementation: Establishing and implementing controls to mitigate identified fraud risks. This might include segregation of duties, authorization procedures, and regular reconciliations.
Monitoring & Detection: Regularly monitoring the effectiveness of controls and actively searching for signs of fraud. This might involve conducting surprise audits, reviewing exception reports, and establishing a whistleblower hotline.
Investigation & Remediation: Investigating any suspected fraud and taking appropriate remedial actions. This might include disciplinary action, legal proceedings, and strengthening internal controls.
Think of it like a layered security system – each control provides another layer of protection. A robust fraud risk management program combines several controls to minimize the probability of fraud occurring and its impact.
Q 26. Describe your experience with conducting follow-up audits.
Follow-up audits are crucial for assessing the effectiveness of corrective actions implemented after a previous audit. My experience involves verifying that identified issues have been addressed and new controls are operating effectively. This typically involves:
Review of Corrective Actions: Examining management’s response to prior audit findings, including the implemented corrective actions and their effectiveness.
Re-testing of Controls: Re-performing tests of controls to verify that the implemented solutions are functioning as intended.
Assessment of Residual Risk: Evaluating the remaining risks after the corrective actions have been implemented.
Reporting: Documenting the findings of the follow-up audit, including an assessment of the effectiveness of the corrective actions and any outstanding issues.
For example, if a previous audit identified a weakness in inventory control, the follow-up audit would focus on verifying that the implemented improvements (e.g., new inventory management system) are working and that inventory discrepancies are minimized.
Q 27. How do you ensure the effectiveness of a compliance training program?
Ensuring the effectiveness of a compliance training program requires a multi-faceted approach focusing on content, delivery, and assessment. I consider these key elements:
Relevant and Engaging Content: The training must cover all relevant regulations and compliance requirements in a clear, concise, and engaging manner. This includes using real-world examples and interactive elements to enhance understanding.
Appropriate Delivery Methods: The method should align with the audience and subject matter. This could include online modules, in-person workshops, or a combination of both, ensuring flexibility and accessibility for all learners.
Regular Assessments: Measuring the effectiveness of the training through assessments, quizzes, or simulations helps ensure comprehension and knowledge retention. Post-training assessments help gauge the impact and identify areas for improvement.
Ongoing Reinforcement: Compliance is not a one-time event. Regular reminders, updates, and refresher courses maintain awareness and reinforce compliance behaviors. This might include periodic email updates or short refresher training sessions.
By combining these elements, a robust compliance training program empowers employees to understand and adhere to relevant regulations, ultimately reducing compliance risks.
Q 28. Describe your experience with using a GRC system.
My experience with GRC (Governance, Risk, and Compliance) systems involves using them to manage and monitor compliance across various organizational functions. These systems provide a centralized platform to streamline compliance processes, track risks, and enhance reporting. My experience includes:
Risk Management: Using the system to identify, assess, and manage risks across different departments and functions. This often involves mapping risks to specific controls and monitoring their effectiveness.
Compliance Management: Using the system to track compliance requirements, manage audits, and ensure adherence to regulations. Features such as automated policy management and reporting tools enhance efficiency.
Governance Processes: Leveraging the GRC system to document and manage governance processes, such as board approvals and policy reviews. Centralized documentation improves transparency and auditability.
Reporting & Analytics: Utilizing the system to generate reports on compliance status, risk profiles, and audit findings. This enables data-driven decision-making and helps organizations effectively manage their compliance programs.
For instance, a GRC system can automate the process of distributing and tracking compliance training completion, allowing for quick identification of employees who haven’t completed the required training.
Key Topics to Learn for Experience with Compliance and Auditing Interview
- Regulatory Frameworks: Understanding relevant laws and regulations (e.g., SOX, HIPAA, GDPR) and their practical implications within different industries.
- Internal Controls: Designing, implementing, and testing internal controls to mitigate risks and ensure compliance. Discuss specific control frameworks like COSO.
- Auditing Procedures: Familiarize yourself with various audit methodologies (e.g., risk-based auditing, data analytics in auditing), including planning, fieldwork, and reporting.
- Risk Management: Identifying, assessing, and mitigating compliance risks, demonstrating a proactive approach to risk prevention.
- Compliance Monitoring and Reporting: Explain the process of monitoring compliance, generating reports, and communicating findings to stakeholders.
- Data Analytics for Compliance: Describe how data analytics can be leveraged to improve the efficiency and effectiveness of compliance and auditing processes.
- Investigative Techniques: Discuss approaches to conducting investigations related to compliance breaches or suspected fraud.
- Communication and Collaboration: Highlight your ability to clearly communicate complex information to both technical and non-technical audiences, and to effectively collaborate with diverse teams.
- Problem-Solving and Critical Thinking: Showcase your ability to analyze complex situations, identify root causes of compliance issues, and develop effective solutions.
Next Steps
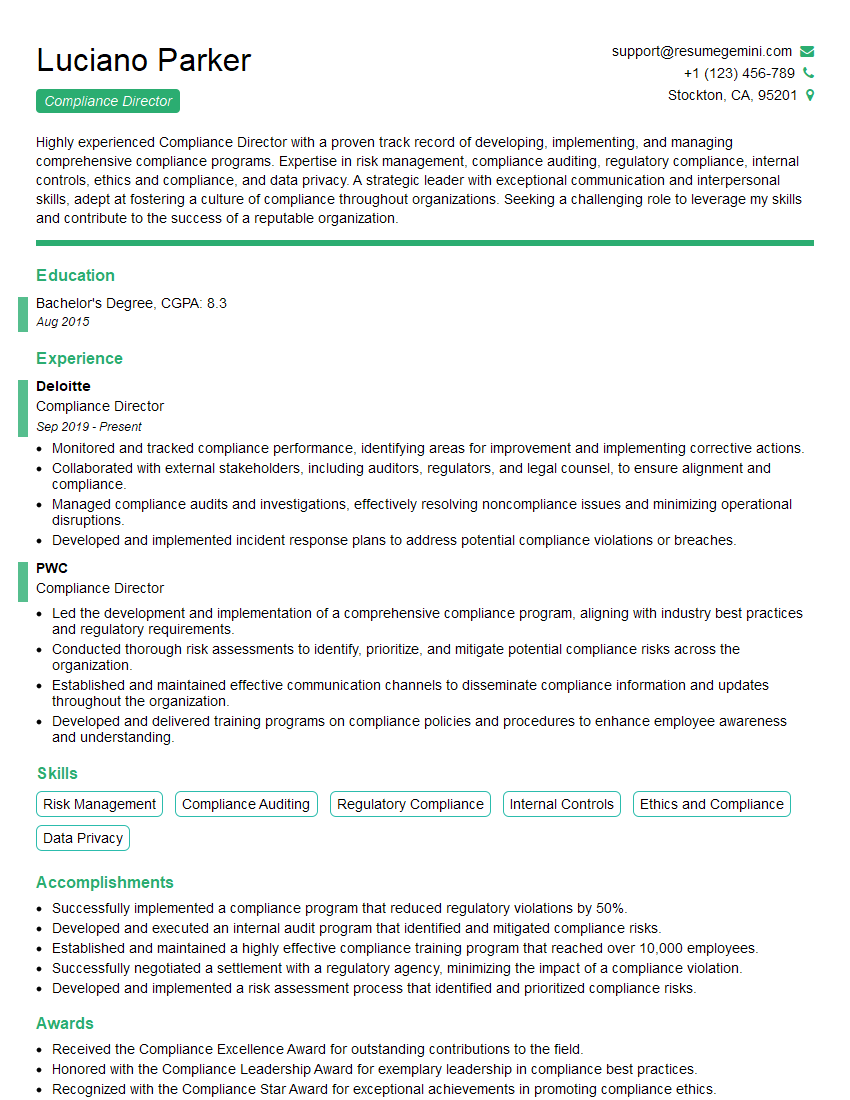
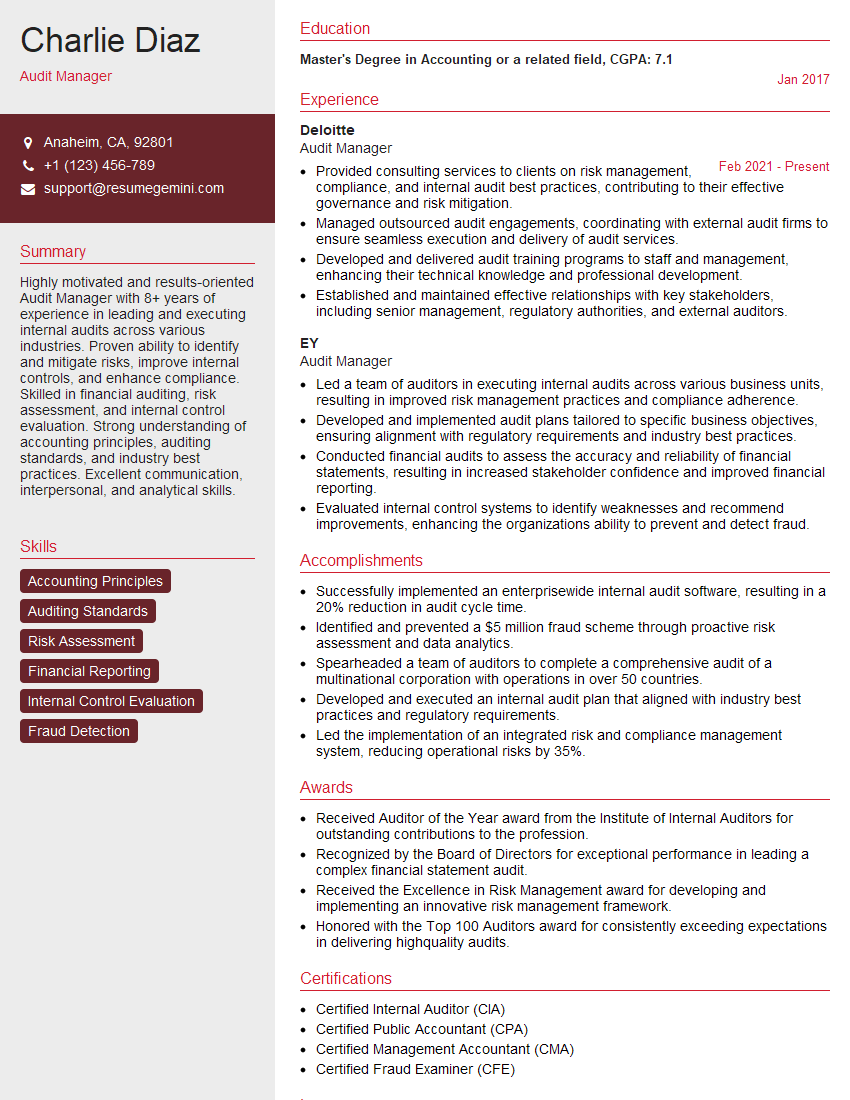
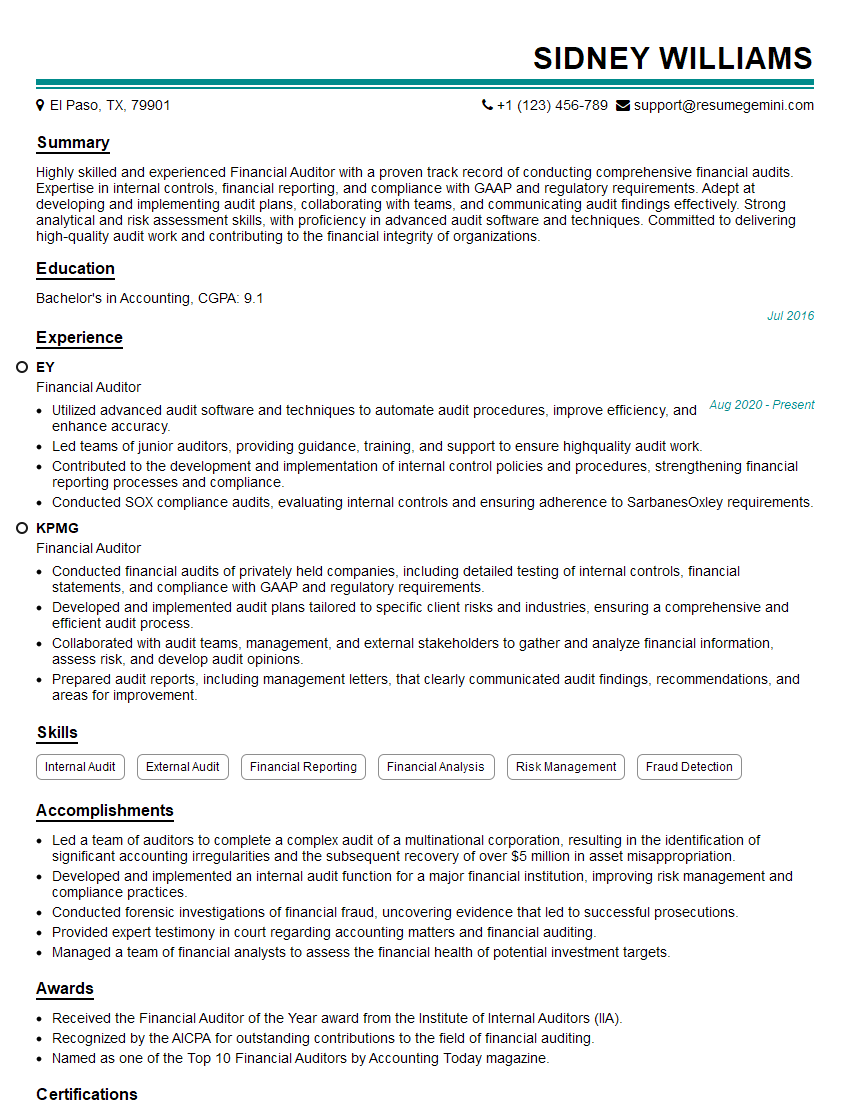
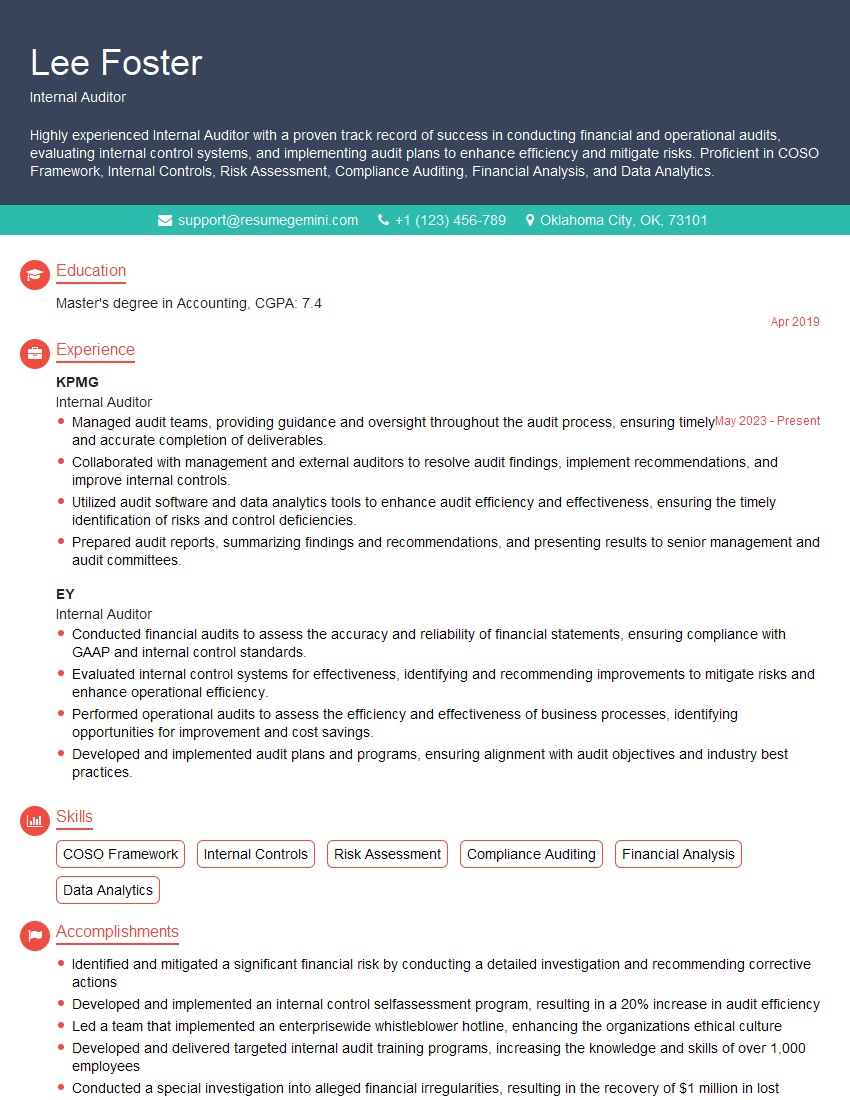
Mastering Experience with Compliance and Auditing opens doors to exciting career opportunities in various sectors, offering high growth potential and rewarding challenges. A strong, ATS-friendly resume is crucial for showcasing your skills and experience to potential employers. To maximize your job prospects, consider using ResumeGemini to craft a compelling resume that highlights your achievements and effectively communicates your expertise. ResumeGemini provides examples of resumes tailored to Experience with Compliance and Auditing, ensuring your application stands out from the competition.
Explore more articles
Users Rating of Our Blogs
Share Your Experience
We value your feedback! Please rate our content and share your thoughts (optional).
What Readers Say About Our Blog
Really detailed insights and content, thank you for writing this detailed article.
IT gave me an insight and words to use and be able to think of examples